A team of researchers from the Ruhr University Bochum in Germany has disclosed a series of new attack methods against signed PDF files.
Dubbed Shadow Attacks, the new techniques allow a hacker to hide and replace content in a signed PDF document without invalidating its signature. The hacker can create a document with two different contents, one that the signer expects to see and one that will be displayed to the recipient of the document.
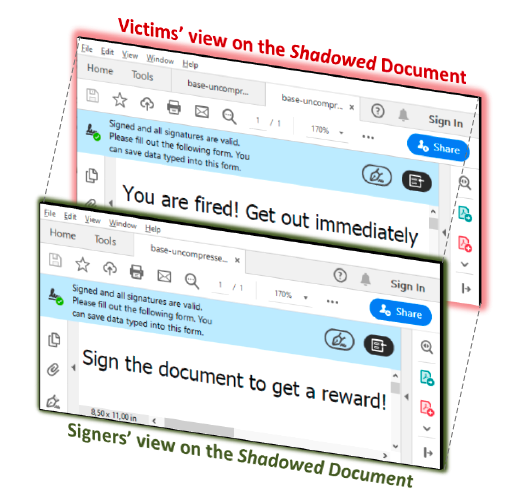
“The Signers of the PDF receive the document, review it, and sign it. The attackers use the signed document, modify it slightly, and send it to the victims. After opening the signed PDF, the victims check whether the digital signature was successfully verified. However, the victims see different content than the Signers,” the researchers explained.
They have tested 28 PDF viewer applications and found that 15 of them were vulnerable to at least one of the attacks, including apps made by Adobe, Foxit, and LibreOffice. These three organizations have already released patches, but many of the impacted vendors either did not respond to the researchers’ messages or they provided no information about the availability of patches.
The same researchers previously disclosed methods for breaking PDF file signatures and making unauthorized changes to signed documents. They have now presented three new attacks on PDF signatures.
Organizations and individuals — this includes governments, researchers and businesses — often sign PDF documents to prevent unauthorized changes. If someone makes modifications to the signed document, its signature should become invalid.
However, the researchers at Ruhr University Bochum have demonstrated three variants of the Shadow Attacks, which attackers can leverage to hide, replace, or hide and replace content in PDF files. The vulnerabilities that allow these attacks are tracked as CVE-2020-9592 and CVE-2020-9596.
The “Hide” variant of the Shadow Attacks involves hiding some content in a PDF behind another layer, such as a full-page image. In an attack scenario described by the experts, the attacker sends the signer a document with an image of an enticing or harmless message on top of the content they want to hide. Once the document has been signed and sent back to the attacker, they can manipulate the file so that the image is no longer rendered by the PDF viewer, which makes the hidden content become visible.
The “Replace” variant of the attack involves appending a new object — an object that is considered harmless but which can impact the way the content is presented — to a signed document.
“For instance, the (re)definition of fonts does not change the content directly. However, it influences the view of the displayed content and makes number or character swapping possible,” the researchers explained.
The “Hide-and-Replace” variant, which the researchers described as “the most powerful,” enables an attacker to change the entire content of a signed document. In this attack, the hacker inserts hidden content and visible content into the document using two objects that have the same object ID, and sends it to the target. Once they receive the signed document, the attacker appends a new Xref table and a new Trailer so that the hidden content is displayed instead of what the victim saw before signing the document.
Related: Nitro Pro Vulnerabilities Expose Many Enterprises to Attacks
Related: Chrome Zero-Day Exploited to Harvest User Data via PDF Files













