Orkus on Monday emerged from stealth mode with a cloud security platform designed to help organizations secure access to data, apps and infrastructure.
Founded in 2017, the San Jose, CA-based company provides a platform that should help enterprises prevent unauthorized access in the cloud, whether it’s caused by insider threats, operator errors or ineffective controls.
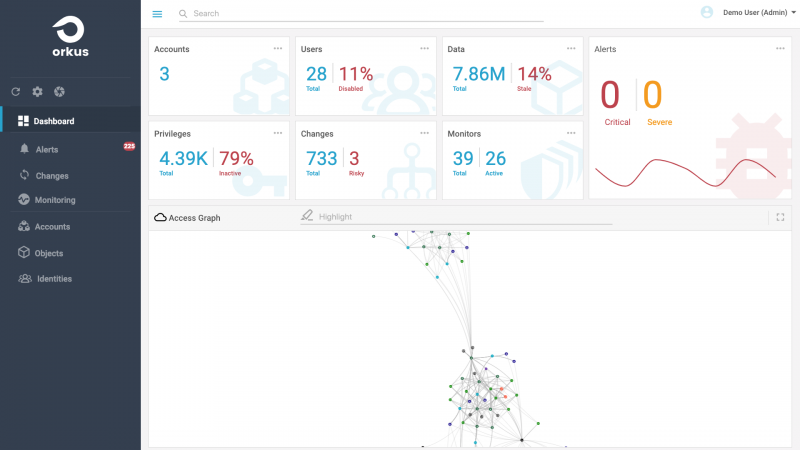
The Orkus Access Governance Platform has four main components: Access Graph, Graph AI, Access Guardrails, and Access Intelligence.

The Access Graph creates a real-time graph of all access relationships, including between data, identities and infrastructure. The graph supports millions of objects and provides continuous visibility and analytics.
The Graph AI leverages machine learning to interpret the access graph and determine access intent and usage. This component can detect risks in an organization’s cloud, including data exposure, insider threats, and unused or stale privileged access, Orkus said.
Access Guardrails automates access governance, allowing security and compliance teams to configure access controls and ensure that sensitive data and critical assets are protected, while maintaining compliance with regulations such as GDPR, PCI and HIPAA.
Finally, the Access Intelligence component allows users to search, analyze and audit access and authorization.
Orkus told SecurityWeek that, to date, it has raised $3.2 million in seed funding in a round led by Aspect Ventures. The company also plans on announcing a Series A funding round next year.
The Orkus Access Governance Platform is immediately available. Pricing is based on the size of the cloud workloads and applications.
The product is already used by financial services company BSI Financial and others.
“Enterprises are rapidly adopting cloud infrastructure for digital transformation initiatives, however one of the key risks holding them back is unauthorized access, because legacy methods of controlling access are not working,” said Manish Kalia, co-founder and CEO of Orkus. “Orkus provides continuous and comprehensive access governance covering all three areas – data, infrastructure and privileged identities. True to its name, the Orkus Access Governance Platform makes strong access governance achievable and sustainable in cloud settings.”
Related: Cloud Security Firm Luminate Emerges From Stealth
Related: Cloud Security Firm ShieldX Emerges From Stealth
Related: RedLock Emerges from Stealth With Cloud Security Platform














