Microsoft this week announced that organizations can now enable their employees to make one-to-one calls on Teams that are protected by end-to-end encryption.
First announced at the tech giant’s Ignite event in March, end-to-end encryption (E2EE) for one-to-one Teams calls is now rolling out to public preview. Organizations can take advantage of the new capability, but IT admins and users will have to manually enable it.
When E2EE is used, conversations are encrypted in a way that prevents anyone, including Microsoft, from intercepting them. However, at this point, only the real-time media flow, which includes video and voice data, is encrypted end-to-end, and the users on both ends of the call will need to enable it.
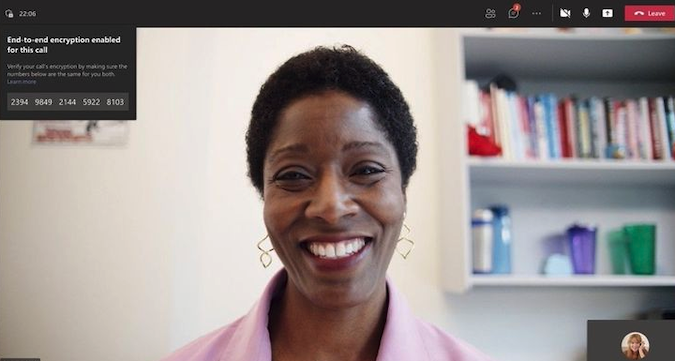
E2EE is available for Teams on Windows, macOS, Android and iOS, and once it has been enabled for an account it can be used across all of a user’s devices. An end-to-end encryption indicator is displayed during a call so that the user knows their conversation is protected.
If users need to use Teams features that are not covered by end-to-end encryption — this includes recording, live caption and transcription, call transfer and merge, and group calls — they have to temporarily disable E2EE.
“In normal call flows, negotiation of the encryption key occurs over the call signaling channel. In an end-to-end encrypted call, the signaling flow is the same as a regular one-to-one Teams call. However, Teams uses DTLS to derive an encryption key based on per-call certificates generated on both client endpoints. Since DTLS derives the key based on client certificates, the key is opaque to Microsoft. Once both clients agree upon the key, the media begins to flow using this DTLS-negotiated encryption key over SRTP,” Microsoft explained.
It added, “To protect against a man-in-the-middle attack between the caller and callee, Teams derives a 20-digit security code from the SHA-256 thumbprints of the caller’s and callee’s endpoint call certificates. The caller and callee can validate the 20-digit security codes by reading them to each other to see if they match. If the codes don’t match, then the connection between the caller and callee has been intercepted by a man-in-the-middle attack. If the call has been compromised, users can terminate the call manually.”
Microsoft noted that even though E2EE is currently only available for one-to-one calls, other features such as group calls and chats are still protected by Microsoft 365 encryption. The company plans on adding E2EE to online meetings as well at some point in the future.
Microsoft has shared instructions on how end-to-end encryption can be enabled for Teams running on desktop and mobile devices.
Related: Zoom Introduces End-to-End Encrypted Phone Calls
Related: Facebook Adds End-to-End Encryption to Calls in Messenger














