The United States has the highest number of malicious domains with names associated with the current coronavirus crisis, a new report reveals.
With the mandatory social distancing rules forcing employees all around the world to work from home, cybercriminals were quick to adapt to the situation and repurpose their attacks. By mid-April, Google was reporting over 18 million COVID-19-themed malware and phishing emails being sent out every day.
Now, Palo Alto Networks’ security researchers say they have identified over 86,600 risky or malicious domains out of 1.2 million domain names registered between March 9 and April 26 that contain keywords related to the COVID-19 pandemic.
On average, just over 1,760 malicious COVID-19-themed domains were created each day during the analysis period, Palo Alto Networks says. The domains covered in the research are those that include keywords such as “coronav”, “covid”, “ncov”, “pandemic”, “vaccine” and “virus.”
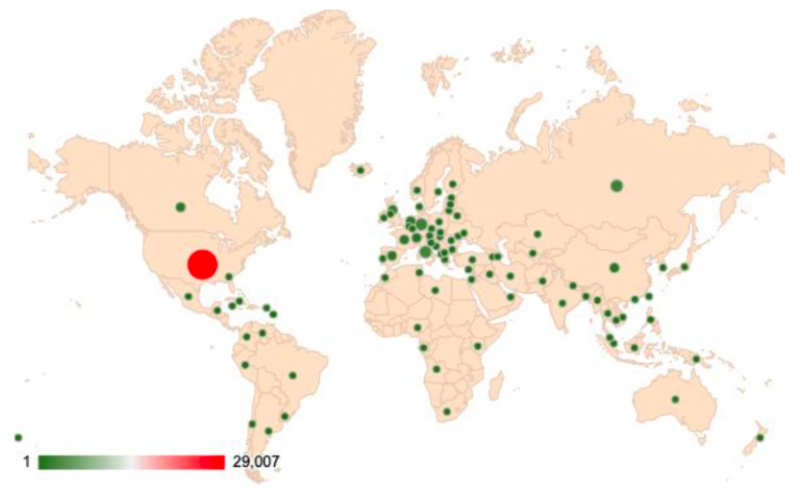
Most of the risky or malicious domains (29,007) are located in the United States, followed by Italy (2,877), Germany (2,564), and Russia (2,456). Most of the domains (79.8%) were used for malware, with phishing (20%) and command and control (0.2%) domains also observed.
More than 56,200 of the newly registered domains were hosted by one of the top four cloud service providers (CSPs): 70.1% (39,494) on Amazon Web Services (AWS), 24.6% on Google Cloud Platform (GCP), 5.3% on Microsoft Azure, and 0.1% on Alibaba Cloud.
Of the 86,600 risky or malicious domains, 2,829 were hosted in public clouds: 79.2% on AWS, 14.6% on GCP, 5.9% on Azure, and 0.3% on Alibaba. By leveraging cloud resources, threat actors can not only evade detection, but also amplify attacks.
In an April 1 report, Cisco revealed that around 4% of the roughly 47,000 domains that included the word “covid” or “corona” were malicious. In addition to “corona”, “virus”, and “covid”, other popular keywords at the time included “wuhan”, “clinics”, “lab”, “tests”, “selftestkit”, “purchase kits” and “helpline”.
Palo Alto Networks researchers also discovered that some of the malicious domains would resolve to multiple IP addresses, while some IP addresses were being used for multiple domains.
“This many-to-many mapping often occurs in cloud environments due to the use of content delivery networks (CDNs) and can make IP-based firewalls ineffective,” they explained. “A blacklisted IP in a layer-3 firewall may fail to block the traffic to/from a malicious domain while unintentionally making many other benign domains unreachable.”
The COVID-19 pandemic also resulted in an increase in cloud adoption, with threats both originating from the cloud and targeting cloud users. As Europol pointed out last week, cyber-attacks, fraud schemes and other activities targeting regular users are expected to continue in the long term.
“With thousands of malicious domains coming online every day, it is imperative to protect every endpoint with continuous monitoring and automatic threat prevention tools. However, cloud-hosted services or applications usually give users less visibility and make network monitoring more challenging,” Palo Alto Networks concludes.
Related: Criminals Quick to Exploit COVID-19 Crisis in Europe
Related: Google Sees Millions of COVID-19-Related Malicious Emails Daily
Related: Vietnamese Hackers Mount COVID-19 Espionage Campaigns Against China















