Malware hunters at Microsoft are calling attention to a nasty macOS malware family that has evolved quickly from a basic information-gathering trojan to a stealthy backdoor with more powerful capabilities.
The macOS malware family, called UpdateAgent, first surfaced just over a year ago with rudimentary infection and data-theft capabilities but researchers have spotted signs the malware is becoming a fully-powered spy toolkit.
In the beginning, around November 2020, Microsoft first observed the macOS threat being used for reconnaissance with basic functions to collect product names, software versions and other system information.
By January 2021, the a newer version added capabilities for fetching secondary payloads from public clouds and a few months later, Microsoft noticed stealthy bypasses of Apple’s security controls, two worrying signs that the gang behind the malware continues to invest heavily to reach victims on Apple’s flagship desktop platform.
[ READ: Apple Ships Urgent Patch for FORCEDENTRY Zero-Days ]
In the latter half of 2021, the malware became even more powerful, collecting more target system data and adding backdoor-type features to execute additional commands. Microsoft even found evidence later that the malware included the ability to modify sudoers list, allowing it to bypass a prompt requiring high privilege user credentials while running UpdateAgent’s downloaded app.
“The latest campaign saw the malware installing the evasive and persistent Adload adware, but UpdateAgent’s ability to gain access to a device can theoretically be further leveraged to fetch other, potentially more dangerous payloads,” Microsoft said in a report documenting the UpdateAgent malware family.
The malware, which is currently being used to siphon money from malicious online advertising, has also been observed bypassing Apple’s Gatekeeper security technology and leveraging existing user permissions to quietly perform malicious activities before deleting the evidence to cover its tracks.
[ READ: Microsoft Disables MSIX Protocol Due to Abuse by Malware ]
“UpdateAgent lures its victims by impersonating legitimate software and can leverage Mac device functionalities to its benefit. One of the most advanced techniques found in UpdateAgent’s latest toolbox is bypassing Gatekeeper controls, which are designed to ensure only trusted apps run on Mac devices,” Microsoft said.
The company also published technical evidence to show UpdateAgent misusing public cloud infrastructure — Amazon S3 and CloudFront services — to host additional payloads.
Redmond shared its findings with Amazon the malicious URLs have since been taken down.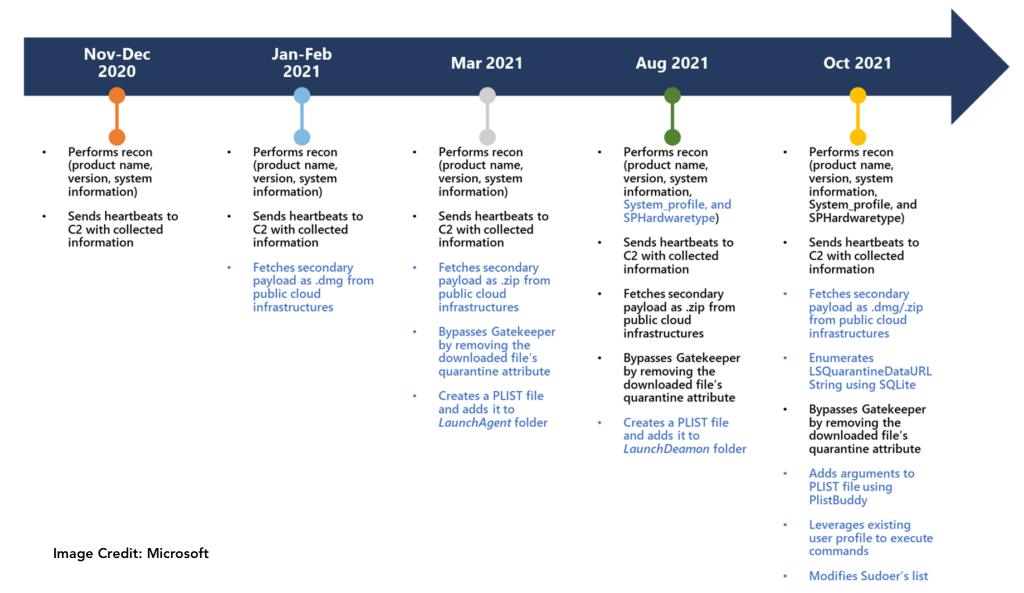
“UpdateAgent is uniquely characterized by its gradual upgrading of persistence techniques, a key feature that indicates this trojan will likely continue to use more sophisticated techniques in future campaigns,” Microsoft warned, noting that the Trojan is likely distributed via drive-by downloads or advertisement pop-ups that impersonate legitimate software applications.
“This action of impersonating or bundling itself with legitimate software increases the likelihood that users are tricked into installing the malware. Once installed, UpdateAgent starts to collect system information that is then sent to its command-and-control (C2) server.
Related: Apple Ships Urgent Patch for FORCEDENTRY Zero-Days
Related: Microsoft Calls Attention to ‘Wormable’ Windows Flaw
Related: Apple Patches ‘Actively Exploited’ Mac, iOS Security Flaw















