Microsoft and CrowdStrike announced on Monday that they are leading an industry effort to map threat actor naming, with the goal of making it easier for the cybersecurity community to align intelligence.
There are hundreds of different threat groups and they can each have dozens of names assigned to them by the researchers and cybersecurity companies that analyze their activities.
For instance, the China-linked group often referred to as APT41 is also tracked as Bronze Atlas, Earth Baku, Wicked Panda and Winnti, among others. The Russia-linked APT28 has at least a dozen other names, including Fancy Bear, Forest Blizzard, Sednit, Sofacy, and Tsar Team.
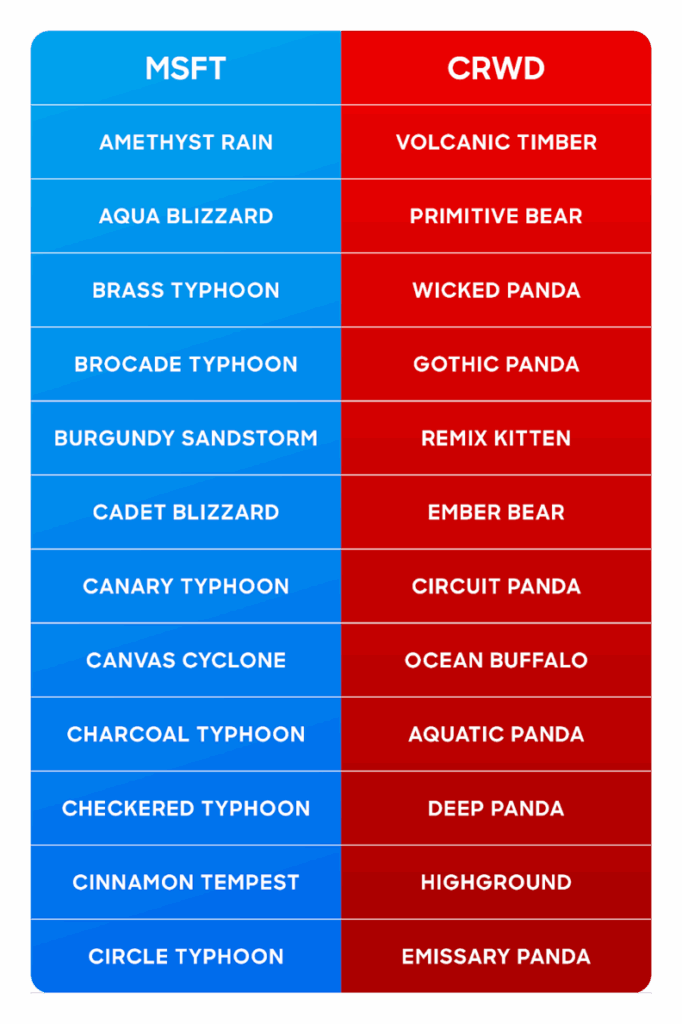
Microsoft has been using a weather-themed naming taxonomy (eg, Blizzard for Russia, Typhoon for China). CrowdStrike has been using an animal-themed naming convention (eg, Panda for China, Bear for Russia, and Spider for cybercriminals). Google Cloud’s Mandiant is known for using the APT[number] and UNC[number] format.
At this point, getting the entire cybersecurity industry to use a single name for each threat group is not practical and may not be possible, CrowdStrike noted, but it’s important to bring clarity to threat attribution across vendors.
As part of the new initiative, Microsoft-assigned names are being mapped to other names assigned to the same threat actor by CrowdStrike and other vendors.
“The alliance will help the industry better correlate threat actor aliases without imposing a single naming standard. It will grow in the future to include other organizations that also practice the art of attribution,” CrowdStrike explained.
“The goal: Deconflicting adversary names to build a cohesive and enduring mapping of existing naming systems to one another. In addition, where telemetry complements one another, there’s an opportunity to extend attribution across more planes and vectors — building a richer, more accurate view of adversary campaigns that benefits the entire community,” it added.
Microsoft pointed out that the initiative should help improve confidence in threat group identification, streamline correlation, and accelerate defender action.
“This effort is not about creating a single naming standard,” Microsoft said. “Rather, it’s meant to help our customers and the broader security community align intelligence more easily, respond faster, and stay ahead of threat actors.”
The tech giant pointed out that Google (Mandiant) and Palo Alto Networks will also contribute to the project.
It’s worth noting that the Malpedia website maintained by Germany’s Fraunhofer Institute for Communication, Information Processing and Ergonomics has been doing a good job over the past years at keeping track of the different names assigned to each threat group, including the malware families they use.
However, the industry could benefit even more from a concerted effort supported by the immense resources of companies such as Microsoft, Google, CrowdStrike, and Palo Alto Networks.
Related: Chinese Hacking Group APT41 Exploits Google Calendar to Target Governments
Related: Russian APT Exploiting Mail Servers Against Government, Defense Organizations
Related: Ransomware Groups, Chinese APTs Exploit Recent SAP NetWeaver Flaws


