Spatial computing attacks targeting VR headsets are rare. Possibly the first ever hack against Apple’s Vision Pro only became public knowledge in the second week of June 2024. But now a researcher has demonstrated a method of delivering any malware to Meta’s Quest 3 headset.
Researcher Harish Santhanalakshmi Ganesan took claims on Reddit that it’s almost impossible to install malware on Quest 3 VR as a personal challenge to explore emerging threat surfaces – he decided to do so without enabling developer mode.
Simple googling told him Meta was using a restricted version of Android Open Source Project (AOSP). “It means I can install any APKs just like installing apps in your Android phone,” he said.
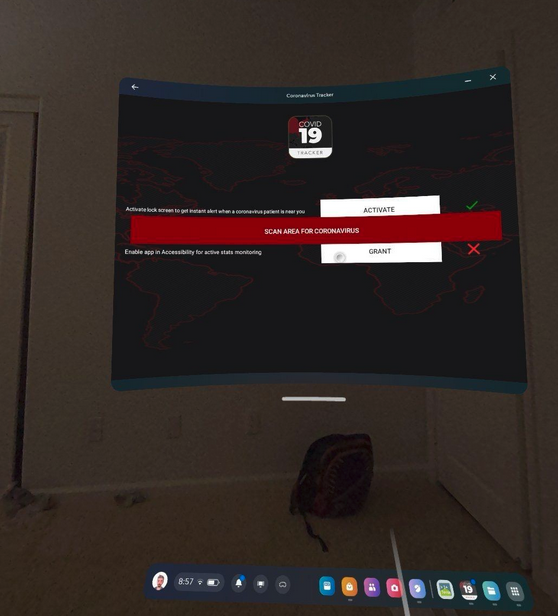
More googling, this time with YouTube, unearthed a methodology using an app from Meta’s App Lab which gives access to native Android’s file manager. “I used this method to install CovidLock ransomware on my headset,” he explained.
CovidLock is a ransomware that targets Android devices. It masquerades as a COVID-19 tracker app and uses permission creep to gain additional permissions. If it gets enough, it locks users out of the device and displays a ransom note.
However, the malware installed by the researcher is irrelevant – the process he discovered could deliver any malware via social engineering.
“This research is not about a vulnerability in Meta Quest 3 rather about an attack surface which allows people to sideload malware without developer options,” he told SecurityWeek. Although he hasn’t published technical details of the method, he believes it would not be difficult for bad actors to replicate the process.
He doesn’t expect Meta to actively respond to his research because it does not technically involve a vulnerability but revolves around social engineering.
Nevertheless, “It means that any attacker could use social engineering to trick a user into installing a malicious app into Quest and make that app a device admin without enabling developer mode. Hypothetically,” he told SecurityWeek, “attackers could create a ransomware and spread it via a YouTube video on how to install third party software without a PC and share the (malicious) APK in the process.”
Since there is no technical vulnerability involved there will likely be no patch. The researcher has publicized his work to warn VR users to beware of social engineering attacks. The primary solution is the same as the advice given to all smartphone users: avoid sideloading.
Related: Spatial Computing Hack Exploits Apple Vision Pro Flaw to Fill Room With Spiders, Bats
Related: Apple Patches Vision Pro Vulnerability Used in Possibly ‘First Ever Spatial Computing Hack’
Related: Virtual Insanity: Protecting the Immersive Online World


