Data allegedly pertaining to over 5 million Panera Bread customers has emerged online after hackers failed to extort the US bakery-cafe chain.
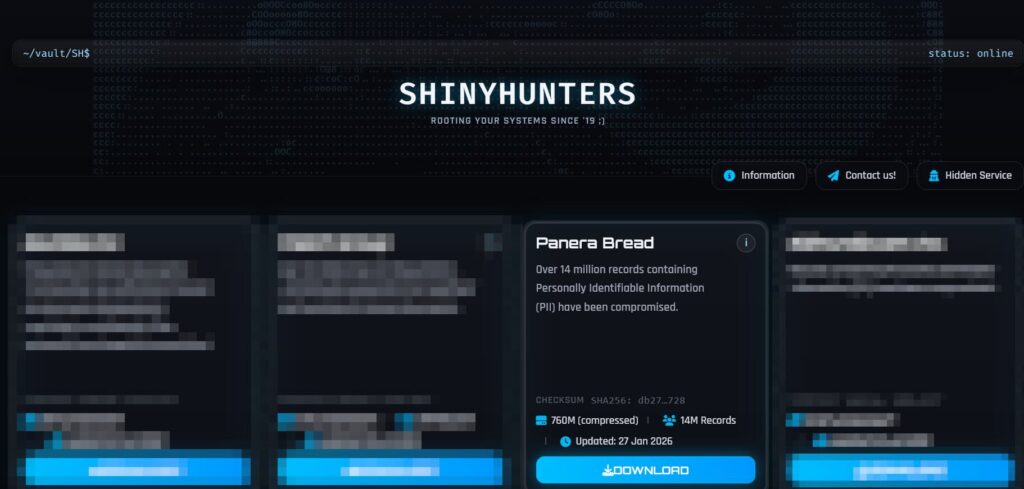
The ShinyHunters extortion group has claimed the theft of roughly 14 million records from Panera Bread, after compromising a Microsoft Entra single-sign-on (SSO) code.
The attack falls in line with recent ShinyHunters attacks that rely on voice phishing (vishing) and SSO authentication to access victim organizations’ cloud-based software-as-a-service (SaaS) environments.
Last week, ShinyHunters published on its Tor-based leak site a 760GB archive allegedly containing the sensitive information stolen from Panera Bread.
According to the data breach notification site Have I Been Pwned, the data was leaked after the hackers failed to extort the food chain.
The archive includes 5.1 million unique email addresses and likely impacts as many Panera customers. Associated information such as names, addresses and phone numbers was also present in the leak.
While it has not responded to a SecurityWeek inquiry on the incident, Panera Bread has confirmed the intrusion, telling Reuters that the hackers stole “contact information”.
“From a defender’s perspective, 5.1 million compromised accounts still represents a massive downstream risk for credential stuffing, phishing, and identity-based attacks well beyond Panera itself,” SOCRadar CISO Ensar Seker said.
ShinyHunters-branded extortion attacks have been escalating recently, with recent reports suggesting the group was setting up to hit over 100 organizations across multiple sectors. Betterment, Crunchbase, and SoundCloud have confirmed the intrusions.
The hackers do not target vulnerabilities but instead rely on vishing to obtain SSO codes, bypass MFA, and access the victims’ SaaS environments for data theft and extortion.
“Vishing-driven SSO compromise bypasses many traditional security controls because authentication flows are trusted by design. If identity becomes the new perimeter, then SSO misconfiguration, MFA fatigue, and help-desk social engineering are now tier-one attack vectors,” Seker said.
Related: Under Armour Looking Into Data Breach Affecting Customers’ Email Addresses
Related: 750,000 Impacted by Data Breach at Canadian Investment Watchdog
Related: Traveler Information Stolen in Eurail Data Breach
Related: After Goldman, JPMorgan Discloses Law Firm Data Breach


