Malicious hackers have started exploiting a critical WinRAR vulnerability disclosed less than one week ago, just as RARLab has released the final version of the update that should patch the flaw.
Researchers at Check Point Software Technologies warned on February 20 that WinRAR, a tool utilized by over 500 million users worldwide, is affected by a remote code execution vulnerability that can be exploited by getting the targeted user to open a specially crafted ACE archive.
The security hole, tracked as CVE-2018-20250, impacts the unacev2.dll library, which is used by WinRAR for unpacking files compressed with the old ACE format. An attacker can exploit the flaw to stealthily extract a file from an archive to an arbitrary location on the system, while also extracting a harmless file to the folder specified by the victim. Code execution can be achieved by extracting a malicious file to the Startup folder in Windows, which would get executed the next time the operating system boots.
When Check Point disclosed its findings, RARLab informed users that version 5.70 beta 1 prevented attacks by completely removing unacev2.dll. The company says the library has not been updated since 2005 and it no longer has access to its source code.
RARLab announced on Tuesday that it has released the final version of WinRAR 5.70, but in-the-wild exploits had already been spotted.
The 360 Threat Intelligence Center of Chinese cybersecurity firm Qihoo 360 revealed on Monday, five days after the flaw was disclosed, that they had seen a malicious email delivering a backdoor by exploiting the WinRAR vulnerability.
The malicious file, stored in an archive with the .zip extension, extracted a file named “CMSTray.exe” to the Windows Startup folder. Less than half of the antivirus engines on VirusTotal detect the threat at the time of writing.
Bleeping Computer has analyzed CMSTray.exe and found that the file connects to an IP address in Mexico, from which it downloads the Cobalt Strike Beacon penetration testing tool. The tool allows the attackers to gain remote access to the targeted device.
ACROS Security’s 0patch service has released an unofficial fix for the WinRAR vulnerability. Unlike the official patch, the one from 0patch does not remove support for the ACE archive format.
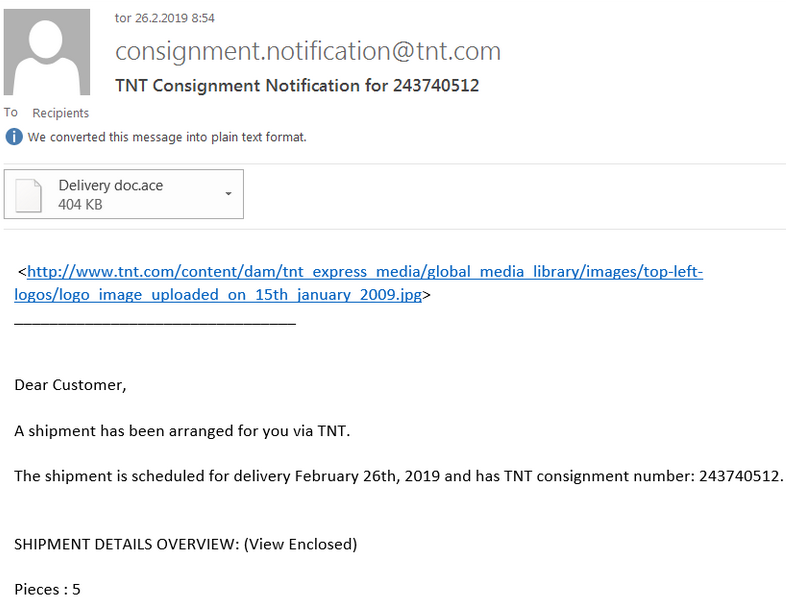
Mitja Kolsek, the CEO of ACROS Security, claims to have seen four types of emails delivering malicious ACE files. The list includes fake invoices, delivery documents, purchase orders, and bank statements.
Kolsek has pointed out that while exploitation of CVE-2018-20250 involves specially crafted ACE files, blocking files with the .ace extension is not an effective protection method as attackers can simply rename .ace files to .rar or .zip.
This is not the first time a WinRAR vulnerability has been exploited by malicious actors. Back in 2014, a flaw in the archiving tool was leveraged in cyber espionage campaigns.
Exploit acquisition firm Zerodium currently offers up to $80,000 for remote code execution flaws in WinRAR.
Related: Drupal RCE Flaw Exploited in Attacks Days After Patch













