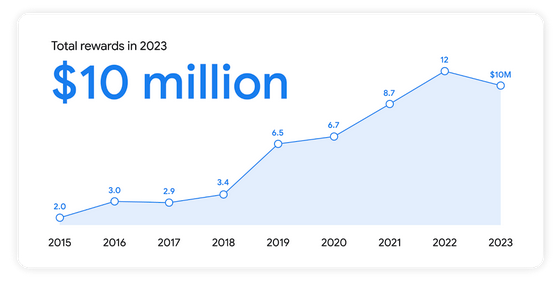
Google on Tuesday announced that it paid out a total of $10 million through its bug bounty programs in 2023, bringing the total amount awarded by the tech giant for vulnerabilities found in its products since 2010 to $59 million.
The total paid out in 2023 is less than the $12 million handed out in 2022, but it’s still a significant amount. The money was earned last year by 632 researchers from 68 countries. The highest single reward was $113,337.
A total of $3.4 million was awarded to researchers who found vulnerabilities in the Android operating system, where the maximum reward has been increased to $15,000.
Google highlighted two conferences: ESCAL8, where researchers earned a total of $70,000 for Wear OS and Android Automotive OS exploits, and Hardwear.io, where researchers earned $116,000 for 50 vulnerabilities in Nest, Fitbit and other products.
The company also ran a live-hacking event focusing on generative AI, where participants earned more than $87,000 for 35 exploits. This includes researchers who recently reported earning $50,000 at the event for their Bard hacks.
In the case of Chrome, Google paid out roughly $2.1 million in bug bounties for 359 vulnerability reports in 2023.
Google’s total bug bounty payouts are comparable to Microsoft’s payouts, which reported recently that it had awarded a total of $63 million since the launch of its first bug bounty program a decade ago.
Related: Google Patches Chromecast Vulnerabilities Exploited at Hacking Contest
Related: Google Expands Bug Bounty Program With Chrome, Cloud CTF Events
Related: Google Announces Bug Bounty Program and Other Initiatives to Secure AI

