A researcher claimed last week that he managed to take control of the country code top-level domain (ccTLD) for the Democratic Republic of Congo after an important domain name was left to expire.
Before the holidays, Fredrik Almroth, founder and researcher at web security company Detectify, decided to analyze the name server (NS) records used by all TLDs. These NS records specify the servers for a DNS zone.
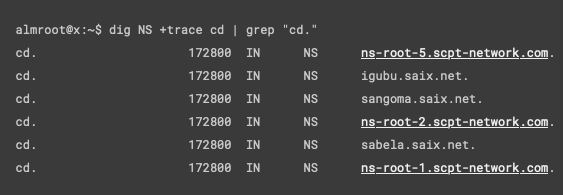
He noticed that a domain named scpt-network.com, which had been listed as a name server for .cd, the TLD for Congo, had been left to expire. Almroth realized that the domain could be highly valuable to a bad actor so he quickly acquired it himself to prevent abuse.
The remaining name servers managing the .cd TLD belonged to South African Internet eXchange (SAIX), which kept the TLD operational. However, gaining control over the scpt-network.com domain could have still allowed a malicious actor to hijack half of the DNS traffic for .cd websites.
Almroth believes the impact could have been significant considering that the African country has a population of approximately 90 million people, as well as the fact that many international organizations have a .cd website.
The researcher noted that a threat actor could have redirected DNS traffic from legitimate sites to phishing or other malicious websites, they could have passively intercepted DNS traffic for surveillance purposes or data exfiltration, or they could have used it for fast fluxing, to hide malicious websites.
Hackers could have also abused this access for remote code execution on local networks, they could have taken control of the domains of high-profile organizations, or they could have launched DDoS attacks against a specific target. They could have also disrupted much of the TLD, Almroth said.
In a blog post published last week, the researcher provided examples of how some of these attacks could have been carried out.
Almroth has been trying to return scpt-network.com to its rightful owner and, in the meantime, name servers have been replaced with scpt-network.net by the administrators of the TLD, who were notified by the researcher in early January.
“The potential implications for DNS hijacking of a ccTLD are widespread and have extreme negative consequences, especially if the attacker has bad intentions,” Almroth explained in his blog post. “This vulnerability affects more than a single website, subdomain, or even a single apex domain. All .cd websites, including those for major international companies, financial institutions, and other organizations that have a .cd domain in Africa’s second most populous country could have fallen victim to abuse, including phishing, MITM, or DDoS.”
Related: DHS Warns Federal Agencies of DNS Hijacking Attacks
Related: Ongoing DNS Hijacking Campaign Targets Gmail, PayPal, Netflix Users
Related: State-Sponsored Hackers Use Sophisticated DNS Hijacking in Ongoing Attacks















