As Anonymous initiated what it said will be the “largest attack ever on government and music industry sites” in response to actions taken by the Justice Department against operators of file sharing site Megaupload.com, downloads of a popular DoS attack tool have spiked.
 While the Denial of Service tool known as the “Low Orbit Ion Cannon” (LOIC) was developed by the “good guys” to stress test websites, it has been a favorite tool of Anonymous to take its targets offline by sending a flood of TCP/UDP packets in an attempt to overwhelm a system and make it inaccessible.
While the Denial of Service tool known as the “Low Orbit Ion Cannon” (LOIC) was developed by the “good guys” to stress test websites, it has been a favorite tool of Anonymous to take its targets offline by sending a flood of TCP/UDP packets in an attempt to overwhelm a system and make it inaccessible.
Interactions seen on Twitter and IRC, made it clear that the action against MegaUpload has sparked many more individuals to get involved in the online protests and download the LOIC to take part in the attacks.
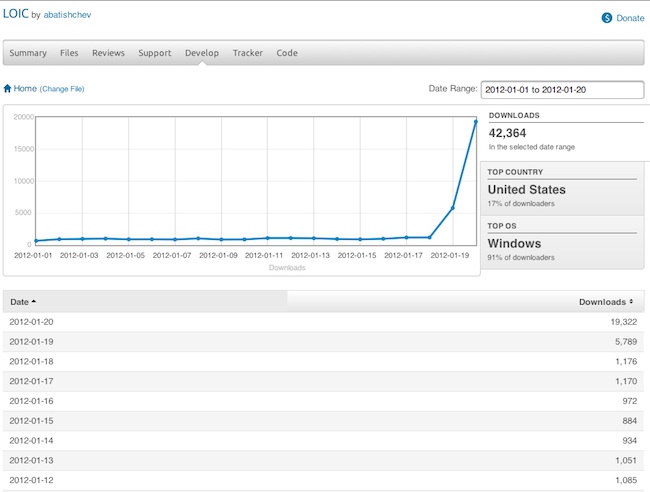
The chart below shows the number of LOIC downloads from Sourceforge so far for the monthly of January 2012. These figures do not include downloads from other sites and sharing, which increases the number even more.
More background on the takedown of Megaupload.Com and the attacks can be found in our previous coverage here.