Cisco has launched an investigation after researchers at F-Secure analyzed two counterfeit Cisco switches that appeared to exploit a previously unknown vulnerability.
The fake Cisco Catalyst 2960-X series switches were used by an IT company. F-Secure was called in to conduct an analysis after the counterfeit devices were discovered in the fall of 2019. The switches stopped working after a software upgrade, which led the IT company to realize that it had been unknowingly using fake Cisco equipment.
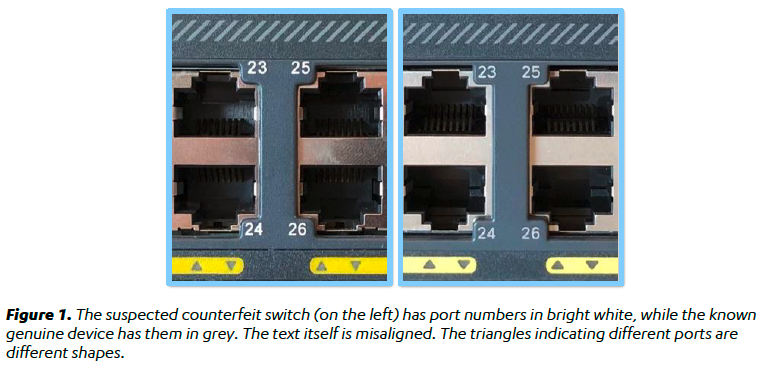
An analysis of the two devices, which appeared to look and work just like authentic Cisco products, revealed the existence of a vulnerability that allowed secure boot mechanisms designed to protect devices against firmware manipulation to be bypassed.
F-Secure told SecurityWeek that it has reported its findings to Cisco, but it has not been able to determine if the vulnerability impacts genuine switches as well.
A Cisco spokesperson said via email that the company “is looking into the researcher’s findings with priority and, if new information is found that our customers need to be aware of and respond to, we will communicate it via our established channels.”
F-Secure’s analysis of the fake Cisco switches focused on the security implications of using such fake devices, particularly if the manufacturer attempted to plant any backdoors.
“While in this case no ‘backdoors’ were identified, the fact the security functions were bypassed means the security posture of the device was weakened. This could allow attackers who have already gained code execution via a network-based attack, for example, an easier way to gain persistence, and therefore impact the security of the whole organization,” F-Secure said in its report.
F-Secure has concluded that the goal of the counterfeiters was likely to make money from their sale, but the company warned that motivated threat actors have been known to use similar approaches to open a backdoor to a company’s systems.
The way the counterfeit equipment was developed suggests that its creator either had access to proprietary engineering documentation from Cisco or they “invested heavily in the complicated process of replicating the original board design files based solely on genuine boards.”
Cisco has warned that counterfeit products pose a serious risk to network quality, performance, safety, and reliability.
“We recommend customers purchase Cisco products from Cisco or through an authorized partner to ensure customers get genuine and authorized Cisco products. To protect our customers, Cisco actively monitors the global counterfeit market as well as implements a holistic and pervasive Value Chain Security Architecture comprised of various security controls to prevent counterfeiting,” Cisco told SecurityWeek. “Cisco also has a Brand Protection team dedicated to detecting, deterring, and dismantling counterfeit activities. Combatting widespread counterfeiting and protecting intellectual property rights are sizable challenges facing the entire technology industry.”
UPDATE. F-Secure says it can confirm that the vulnerability impacts genuine Cisco devices as well.
Related: Cisco Patches High Severity Vulnerabilities in Security Products
Related: Cisco Patches Dozen Vulnerabilities in Industrial Routers













