Documents published by WikiLeaks on Thursday provide details on a tool allegedly used by the U.S. Central Intelligence Agency (CIA) to hack routers and access points.
Dubbed CherryBlossom, the tool is described by its developers as a system designed for monitoring a target’s Internet activity and delivering software exploits via wireless networking devices. WikiLeaks said the tool was developed and implemented by the CIA with the help of a US-based nonprofit research center called SRI International.
The leaked documents show that the tool has been under development since at least 2006 and at one point it worked on roughly 200 device models from more than 20 vendors, including 3Com, Accton, Cisco, Ambit, AMIT, Asus, Apple, Breezecom, D-Link, Gemtek, Global Sun, Linksys, Orinoco, Planet Tec, Senao, US Robotics and Z-Com.
The main component of CherryBlossom is Flytrap, the implant deployed on the targeted device. Documentation made available by WikiLeaks shows that this implant can be delivered through several methods. One method involves a tool called Claymore, which allows users to remotely deliver a firmware update containing the implant.
The implant can also be delivered via the targeted device’s firmware upgrade functionality, a method that requires knowledge of the administrator password and wireless security credentials. Flytrap can also be deployed using a specialized wireless upgrade package that works on some devices that don’t allow wireless firmware updates, and via physical access to the targeted router – typically via the supply chain.
Once the implant is in place, it communicates with a command and control (C&C) server dubbed CherryTree. Flytrap is controlled via a web-based user interface named CherryWeb.
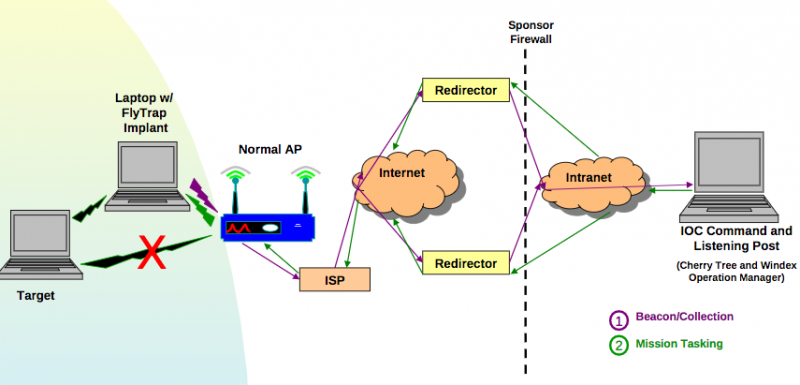
Users can instruct the implant to harvest email addresses, VoIP numbers and chat usernames, copy network traffic, redirect the browser, proxy the victim’s network connection, and execute other applications.
WikiLeaks has been publishing CIA files, which are part of a leak dubbed “Vault 7,” nearly every week since March 23. The tools exposed by the whistleblower organization include ones designed for replacing legitimate files with malware, hacking Samsung smart TVs, MitM tools, a framework used to make malware attribution and analysis more difficult, and a platform for creating custom malware installers.
Symantec and Kaspersky have found links between the tools exposed by Wikileaks and the malware used by a cyber espionage group tracked as “Longhorn” and “The Lamberts.”
Related Reading: If the CIA Isn’t Secure, Who Is?
Related Reading: Industry Reactions to CIA Hacking Tools
















