A team of researchers from China’s Pangu Lab on Wednesday published a 50-page report detailing a piece of Linux malware allegedly used against many targets by the threat actor known as the Equation Group, which has been linked to the U.S. National Security Agency (NSA).
It’s not uncommon for cybersecurity companies in the United States to publish reports detailing the tools and activities of threat actors linked to the Chinese government, and now a group of Chinese researchers have released a report detailing a piece of malware tied to the U.S. government.
Pangu Lab is a research project of Pangu Team, which is best known for its iPhone jailbreaks. An iOS exploit earned them $300,000 last year at a major Chinese hacking contest.
The backdoor detailed by the researchers this week has been dubbed Bvp47 and it was first discovered in 2013 while investigating an incident affecting a Chinese government organization. They determined at the time that it appeared to be a “top-tier APT backdoor,” but further investigation required a private key that they could not obtain.
The malware was named Bvp47 based on the “Bvp” string commonly found in its source code and the “0x47” value used in an encryption algorithm.
In 2016 and 2017, a mysterious group calling itself The Shadow Brokers leaked vast amounts of data allegedly stolen from the NSA-linked Equation Group, including many hacking tools and exploits. Within those leaks, Pangu Lab researchers found the private key they needed to further analyze the Bvp47 backdoor.
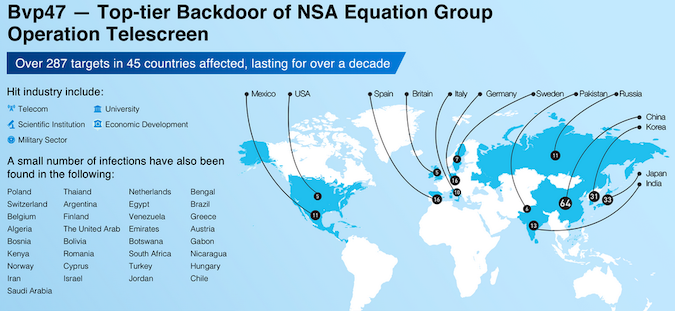
According to the researchers, the malware was used as part of a campaign they have dubbed “Operation Telescreen,” which appears to have targeted nearly 300 entities across 45 countries over a period of more than a decade.
The backdoor was used against organizations in the telecom, higher education, military, scientific, and economic development sectors in North America, Europe and Asia, Pangu Lab said.
Bvp47 appears to be designed to provide its operators long-term control over compromised devices and it includes rootkit, security feature bypass, anti-forensics, self-deleting and other capabilities.
“The tool is well-designed, powerful, and widely adapted,” Pangu Lab said. “Its network attack capability equipped by 0day vulnerabilities was unstoppable, and its data acquisition under covert control was with little effort.”
Pangu Lab’s report — in addition to a technical description of Bvp47 — attempts to highlight links between the malware, the Equation Group and the NSA.
Related: Researchers Dive Into Equation Group Tool ‘DoubleFeature’
Related: Unknown Chinese APT Targets Russian Defense Sector
Related: VMware Patches Vulnerabilities Disclosed at Chinese Hacking Contest















