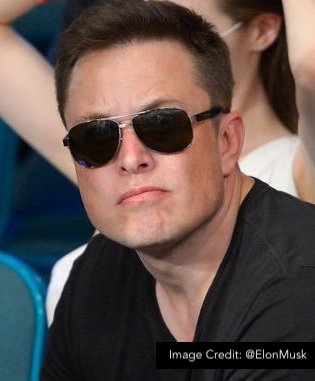
NEWS ANALYSIS: Elon Musk’s stated mission to “authenticate all humans” and defeat the spam bots on Twitter could spur cybersecurity tech innovation around identity, multi-factor authentication and botnet detection.
Elon Musk’s sudden deal to purchase Twitter has triggered optimism in some quarters that the mission to “authenticate all humans” and defeat spam bots will spur technology innovation at a company that has historically struggled with cybersecurity.
Following the announcement of the agreed $44 billion transaction on Monday, Musk publicly positioned the deal as an attempt to protect free speech at a company that manages the world’s digital town square but industry watchers are paying closer attention to Musk’s larger goals around security technology innovation.
“I also want to make Twitter better than ever by enhancing the product with new features, making the algorithms open source to increase trust, defeating the spam bots, and authenticating all humans,” Musk said, without elaborating.
[ READ: Why Are Users Ignoring Multi-Factor Authentication? ]
Twitter has focused its engineering energy on a series of oddball features (things like NFT profile pictures, $2.99 Twitter Blue subscriptions and Super Follows for content creators), while struggling to manage bot-driven disinformation campaigns, failing to encrypt direct messages, and struggling to get users to adopt multi-factor authentication protection.
Even worse, the company has struggled with consistent security leadership, hiring and firing multiple CISOs even as nation-state adversaries target Twitter’s massive user base with computer-generated disinformation campaigns.
Twitter has played whack-a-mole with disinformation activities associated with nation-state actors from Russia and Iran but it has proven difficult to properly scale a response to APTs that use the platform to disrupt elections activities around the world.
“Even if you don’t like the guy, you have to root for Twitter to beat the bots,” said one prominent CISO interviewed by SecurityWeek on Tuesday. “I think we will all benefit from any security features they [Twitter] can create.”
Jamie Moles, a senior technical manager at ExtraHop, said the bot-elimination mission could have spinoff benefits for the entire industry. “While this seems like a Sisyphean task, if he’s successful, the methods used by Twitter to eliminate bots from the platform may generate new techniques that improve the detection and identification of spam emails, spam posts, and other malicious intrusion attempts,” Moles said.
If Musk and his team can train AI to be more effective in combating this, it may well be a boon to security practitioners everywhere,” Moles added.
“Identity is one area I expect to see movement. In addition to just detecting bots and spam better, I think we will see Twitter do a better job around verifying humans. There are a lot of things to fix there,” said one CISO who requested anonymity because his company does security-related business with Twitter.
Industry watchers also expect to see the company improve the multi-factor authentication (MFA) adoption numbers among its massive user base. A transparency report released by Twitter in January this year showed that barely 2.3 percent of all active Twitter accounts had enabled at least one method of two-factor authentication. Even worse, out of that paltry 2.3 percent of all users who opted to turn on the password-verification feature, 80 percent used the weaker SMS-based authentication, which is known to be susceptible to phishing and SIM-hijacking attacks.
Twitter has publicly acknowledged this is a significant industry-wide hiccup, describing poor MFA uptake as an “unfortunate challenge across the industry” but the company has done a poor job of promoting and marketing these tools to non-technical end users.
Security experts are also calling attention to the absence of end-to-end encrypted DMs (direct messages) on Twitter, an in-demand feature that helps to mitigate eavesdropping and insider attacks. This is another area that’s ripe for innovation at Twitter and will earn the company credibility with privacy rights advocates who long argue that private communications on public platforms should be kept away from prying eyes.
If Twitter can build a reliably secure platform with a new approach to distinguishing between human and bot traffic and fresh flavors of MFA and encryption, this could be a big win for the entire industry and users around the world.
Related: Hackers Used Internal Twitter Tools to Hijack Big-Name Accounts
Related: Why Are Users Ignoring Multi-Factor Authentication?
Related: Experts Say Twitter Breach Troubling, Undermines Trust
Related: Peiter ‘Mudge’ Zatko Named Head of Security at Twitter


