This year, Cross-Site Scripting (XSS) continued to be the most common vulnerability type and received the highest amount of rewards on HackerOne, the hacker-powered vulnerability reporting platform says.
In a report published this week, HackerOne reveals that XSS flaws accounted for 18% of all reported issues, and that the bounties companies paid for these bugs went up 26% from last year, reaching $4.2 million (at an average of just $501 per vulnerability).
Extremely common and difficult to eliminate, XSS flaws often get embedded into web applications’ code and could be exploited for account compromise or the theft of sensitive information, including bank account numbers, credit card data, passwords, personally identifiable information (PII), and more.
The second most awarded vulnerability type in 2020, HackerOne says, is Improper Access Control, which saw a 134% increase in occurrence compared to 2019, with a total of $4 million paid by companies in bug bounty rewards.
Information Disclosure maintained the third position it held in last year’s report, registering a 63% year-over-year increase. With $3 million paid by organizations to mitigate them over the past year, Server-Side Request Forgery (SSRF) vulnerabilities ended up on the fourth position.
“Previously, SSRF bugs were fairly benign and held our seventh place spot, as they only allowed internal network scanning and sometimes access to internal admin panels. But in this era of rapid digital transformation, the advent of cloud architecture and unprotected metadata endpoints has rendered these vulnerabilities increasingly critical and sheds light on the risk of cloud migrations done wrong,” HackerOne said.
Rounding up top five is Insecure Direct Object Reference (IDOR), followed by Privilege Escalation, SQL Injection, Improper Authentication, Code Injection, and Cross-Site Request Forgery (CSRF).
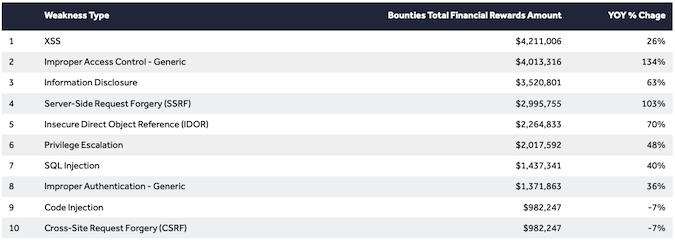
Fifth in 2019 but seventh in 2020 is SQL injection, as it started to drop in occurrence. OWASP considers SQL Injection as being one of the worst threats to web application security, leading to devastating attacks in which sensitive data such as business data, intellectual property, and customer information could be compromised.
In just one year, organizations paid $23.5 million via HackerOne to those who submitted valid reports for these 10 vulnerability types.
To date, the hacker-sourced platform paid $107 million in bug bounties, with more than $44.75 million of these rewards being paid within a 12-month period, HackerOne announced in September 2020.
“Finding the most common vulnerability types is inexpensive. Of the top 10 most awarded weakness types, only Improper Access Control, Server-Side Request Forgery (SSRF), and Information Disclosure saw their average bounty awards rise more than 10%. The others fell in average value or were nearly flat. Unlike traditional security tools and methods, which become more expensive and cumbersome as goals change and attack surface expands, hacker-powered security is actually more cost-effective as time goes on. With hackers, it’s becoming less expensive to prevent bad actors from exploiting the most common bugs,” HackerOne Senior Director of Product Management Miju Han said.
Related: HackerOne Paid Out Over $107 Million in Bug Bounties
Related: Verizon, PayPal, Uber Paid Out Most Through Bug Bounty Programs on HackerOne
Related: Sony Launches PlayStation Bug Bounty Program on HackerOne














