Boeing is investigating recent claims made by the LockBit ransomware gang that large amounts of data were exfiltrated from the aerospace giant’s network.
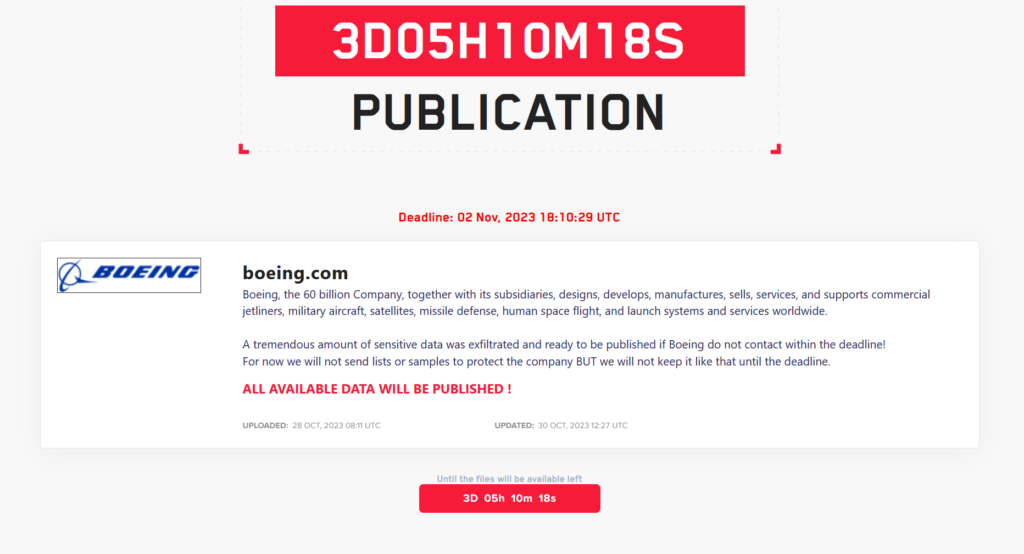
An entry added to the cybercrime group’s leak site on Friday alleges that sensitive data was stolen from the company, threatening to publish it unless Boeing contacts the gang to negotiate a ransom.
“A tremendous amount of sensitive data was exfiltrated and ready to be published if Boeing do not contact within the deadline,” the post reads.
The LockBit ransomware group has not shared samples of the allegedly stolen data, supposedly to protect the manufacturer.
Boeing has launched an investigation into the matter, but has yet to confirm a potential compromise or share any details on the incident.
“We are assessing this claim,” Boeing said, responding to a SecurityWeek inquiry on the matter.
LockBit has been active since at least 2020, operating under the ransomware-as-a-service (RaaS) business model, with several major versions of its malware identified to date.
LockBit affiliates have been seen targeting organizations in critical infrastructure, energy, government, financial services, food and agriculture, healthcare, manufacturing, and other sectors.
Used in one-fifth of the ransomware attacks observed in Australia, Canada, New Zealand, and the US last year, LockBit is believed to have launched approximately 1,700 attacks against US entities and to have received roughly $91 million in ransom payments from them.
The cybercrime gang is known for listing on its leak site the names of victims that refuse to pay up and has been observed engaging in secondary extortion after compromising a third-party provider.
The group typically uses freeware and open source tools in attacks, and is also known for exploiting numerous vulnerabilities, including newly reported ones.
Related: LockBit Affiliate Deploys New 3AM Ransomware in Recent Attack
Related: US Government Warns Organizations of LockBit 3.0 Ransomware Attacks
Related: Russian National Arrested, Charged in US Over Role in LockBit Ransomware Attacks

















