Law enforcement agencies in the United States and Europe have disrupted SocksEscort, a malicious proxy service that facilitated criminal activities.
These proxy services enable users to hide their identity and bypass security systems. In the case of SocksEscort, it has been used for various types of cybercrime, including DDoS attacks, ransomware attacks, and the distribution of child abuse materials.
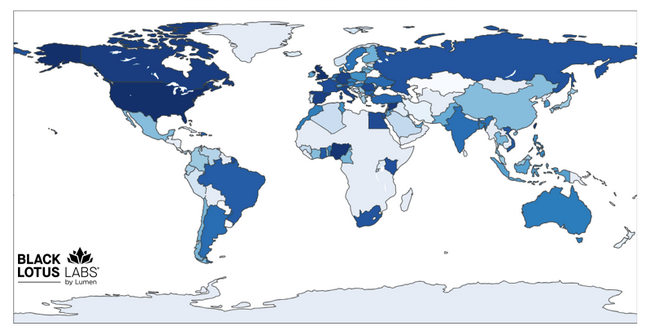
According to Europol and the US Justice Department, SocksEscort has been powered by compromised routers and other IoT devices, with roughly 363,000 IP addresses from 163 countries linked to the cybercrime service since 2020.
In February 2026, just before the takedown operation was initiated, SocksEscort was supported by approximately 8,000 hacked routers, including 2,500 in the US.
Lumen Technologies, whose Black Lotus Labs assisted the disruption efforts, said “SocksEscort maintained an average size of approximately 20,000 distinct victims weekly, with communications routed through an average of 15 command-and-control nodes.”
Authorities estimate that SocksEscort customers paid a total of more than $5.7 million for the proxy service, and US Justice Department data indicates many users profited substantially from it, with some defrauding victims of hundreds of thousands or even $1 million in individual schemes.
Europol reported that “law enforcement agencies successfully took down and seized 34 domains as well as 23 servers located in seven countries. In addition, the United States froze a total of USD 3.5 million in cryptocurrency. The infected modems used to offer the proxy service have been disconnected from the service.”
The FBI on Thursday issued an alert for the AVrecon malware that has powered the SocksEscort service. The agency said the proxy service’s operators exploited known vulnerabilities in routers and IoT devices to deploy the malware and create a botnet.
“SocksEscort uses AVrecon malware to target approximately 1,200 device models manufactured by Cisco, D-Link, Hikvision, MicroTik, Netgear, TP-Link, and Zyxel,” the FBI said. “The vast majority of observed devices infected with AVrecon malware are small-office/home-office (SOHO) routers infected using critical vulnerabilities such as Remote Code Execution (RCE) and command injection.”
The agency has shared information on the AVrecon malware’s distribution, execution, persistence, and communication, providing indicators of compromise (IoCs) and recommendations for securing devices.
News of the SocksEscort takedown comes shortly after Europol, Microsoft, and cybersecurity companies announced a joint effort to take down the phishing-as-a-service platform Tycoon 2FA.
Related: SystemBC Infects 10,000 Devices After Defying Law Enforcement Takedown
Related: RaccoonO365 Phishing Service Disrupted, Leader Identified
Related: 1,000+ Servers Hit in Law Enforcement Takedown of Rhadamanthys, VenomRAT, Elysium