
Cyber-criminals are increasingly crafting attacks and targeting specific employees to maximize their ill-gotten gains. Who better to target than the folks who manage lots of money?
Barracuda Labs recently detected a spam campaign targeting hedge fund managers, Dave Michmerhuizen and Luis Chapetti, security researchers at Barracuda Networks, wrote Wednesday on the company’s Internet Security blog. Like other targeted attacks, the criminals behind this campaign took pains to create an email that would pique the recipient’s interest and open the attachment.
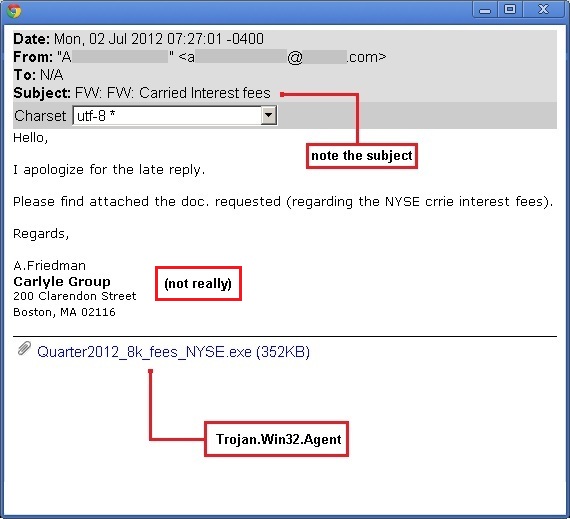
The pitch in the attack email was short and simple, offering advice about carried interest feed, an account mechanism used by hedge and private equity funds to return income to funds. Lately, its tax status has been under discussion.
“For this reason, any email purporting to have information about carried interest fees is likely to raise the curiosity of financial professionals,” Michmeerhuizen and Chapetti wrote.
Like other targeted attacks, the short email pitch came with an executable file as an attachment. The file, actually a Trojan, had a filename that seemed relevant to financial professionals. However, in this case, attackers were sending an executable, not a PDF or RTF document.
Opening and running the attachment, which a user should never do, displays a file that contained actually relevant information, according to the post. While the attachment is open and running, it installs a keylogger in the background.
The keylogger captures keystrokes and later loads them to a remote server using FTP, Michmeerhuizen and Chapetti wrote. Researchers were able to look at all the directory containing all the harvested information on the remote server. Each folder had the name of the computer which had been infected and contained the keylogger files sent from that machine.
“Never trust an attachment sent to you in email, even if the source appears reputable,” the Barracuda researchers said in the post.
The installed security suite on the computer may not be able to detect these attachments as malicious because criminals are going to great lengths to avoid detection. In cases like this, recipients should save the file without running it and send it to the virus scanning service virustotal.com, Michmeerhuizen and Chapetti wrote.
The service scans the file against popular security products to figure out whether it is detected by major antivirus and scanning engines. As of today, only 11 out of 42 products, including eSafe, Kaspersky, McAfee, Symantec, and Trend Micro, were able to detect this particular attachment, according to VirusTotal.

