Researchers at Symantec have uncovered a way to fool Facebook users into defeating the social network’s defense against cross-site request forgery attacks.
Known as CSRF for short, cross-site request forgery attacks are a type of attack where the attackers use an authenticated session on a Website to perform unauthorized actions on the site. Guarding against these attacks are Anti-CSRF tokens, which are typically random, unique tokens generated by the Website. In order to generate a CSRF token, the attackers have to figure out the Anti-CSRF token, which in turn makes the attacks harder to execute.
The scheme takes a bit of trickery on the part of the attacker. According to Symantec, the attack starts with a message inviting users to watch a video. From there, if users click on the link, they will be taken to a fake YouTube page where a window will pop up requiring the person to pass a “YouTube Security Verification” test. When the user clicks on the “Generate Code” link, a request is sent to 0.facebook.com/ajax/dtsg.php. This request will return JavaScript code the user will then be prompted to paste into the “Insert Verification Code” box.
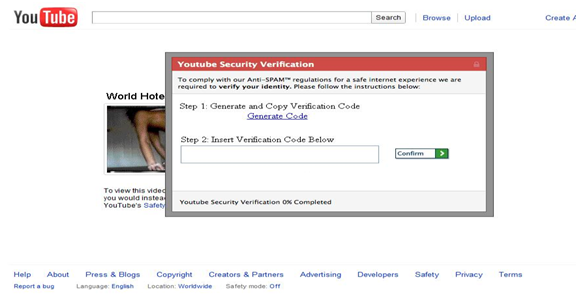
“So what is so special about this JavaScript Code? The answer is the Anti-CSRF token called ‘fb_dtsg’,” blogged Nishant Doshi, security analyst at Symantec. “In order to prevent CSRF attacks, Facebook pages have a unique per session token called “fb_dtsg”. The request to “facebook.com/ajax/dtsg.php” returns JavaScript code containing the “fb_dtsg” token… In this case the attacker’s third-party site receives this Anti-CSRF token when the user copy and pastes the JavaScript code and clicks Confirm. The attacker is now in a position to perform CSRF attacks.”
As a result of the CSRF attack, a malicious link is posted on the victim’s Facebook page using the stolen token, potentially further propagating the attack.
Facebook spokesperson Frederic Wolens told SecurityWeek that engineers have been working to deal with the problem of Anti-CSRF token hijacking by adding enforcement mechanisms to shutdown malicious pages and fake accounts. In addition, Facebook has also been working with browser vendors to “ensure their features are not being maliciously exploited.”
In addition to the CSRF attack, Facebook security was also put under the lens recently when security researcher Nathan Power discovered a way to upload executables to Facebook. Essentially, he uncovered a bug that enabled him to send a Facebook message with an attachment. Facebook downplayed the attack however, noting the Messages feature does not rely solely on string matching to detect potentially malicious files but also has antivirus protection scanning every message. Power’s attack, as demonstrated, would only allow one user to send an obfuscated renamed file to another user, but would not automatically execute on the recipient’s machine.
This means that just like with the Anti-CSRF token stealing scheme success for the attacker relies on social engineering.
“Educating users is one of the primary tools to combat social engineering attacks,” said Ben Greenbaum, senior research manager for Symantec Security Response. “Users should be taught what to watch out for and to avoid divulging any potentially sensitive information online.”







