Patent Lawsuit Against Apple Forces Change in iOS VPN On Demand Functionality – Enterprises and Vendors Scramble
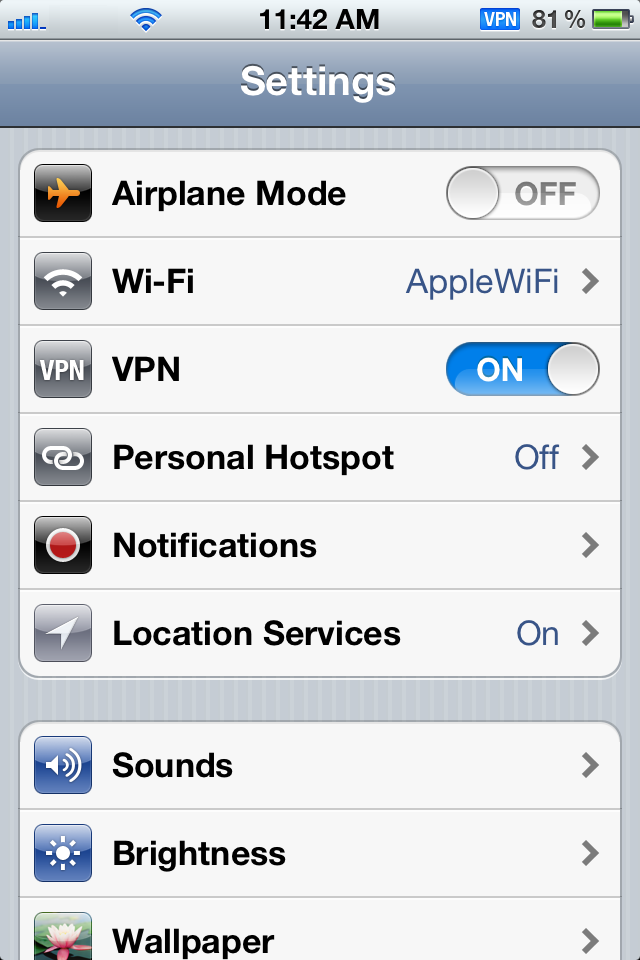
Next to Android, Apple’s iOS is the most widely used mobile operating system in the world. Enterprises and SMBs rely (sometimes with little choice otherwise) on it to enable employees to work anywhere at anytime. A recent lawsuit against Apple has forced the tech giant to alter the way iOS handles VPN traffic, and will be changing the behavior of the “VPN On Demand” function for iOS devices using iOS 6.1 and later. As a result, enterprises and security vendors are going have to scramble in order to find scalable solutions.
The lawsuit against Apple made headlines because it was focused on FaceTime. The court case happened because VirnetX, a patent troll in Nevada that has already won similar cases against Microsoft and who recently filed for a new trial against Cisco, claimed that Apple was abusing its intellectual property. However, other aspects of that lawsuit addressed the On Demand VPN features that were shipped with iOS.
 Its VPN was one of the key features that enabled Apple to establish itself in the corporate network, and so iPhones and iPads were instantly added as a new endpoint for better or for worse.
Its VPN was one of the key features that enabled Apple to establish itself in the corporate network, and so iPhones and iPads were instantly added as a new endpoint for better or for worse.
These days, mobile is the hot topic in the business world because these devices offer fast access to data and other information. These always on, Internet ready assets have been proven to increase productivity, as they allow people to share resources and information faster. Forms stored and processed on a phone can close sales quicker, product data is shared in real-time during a client briefing, and business contacts are available at the touch of a button, thanks to cloud-based applications.
At the same time, the opposite side of the coin is that mobile exposes the organization to a new level of risk. Criminals target these devices to gain access to the same data and other information that make them valuable in the first place. In response to this, programs focused on Mobile Device Management entered the information security arena. Data is a core feature in any MDM product. It you can’t protect the data while it is at rest or in motion, then why protect the device at all?
Apple understood this, and developed the tools needed to enable On Demand VPN. If the environment is configured correctly, and the device is provisioned properly, corporate users with an iOS device had an automatic option that securely interacts with the network. This isn’t something they can disable, which adds a bonus, as it is lowering the risk of accidental exposure.
As soon as an iOS device detects the proper settings, be it a domain or DNS configuration, a VPN connection is enabled and work progresses as normal. Now that’s gone, and it’s going to be a nightmare for many organizations.
It isn’t just about inconvenience. Manual VPN connections will cause usability problems to be sure, but the inconvenience factor already exists for the most part – and that’s a separate issue really. Apple’s pending changes will only aggravate them. The real problem that the lawsuit and VirnetX has caused, is the fact that employees will be able to choose when VPN connections are established (if it’s established at all), and existing secure communication channels will be cutoff.
This can’t be stressed enough, if the end user has the ability to pick when VPN is used – it won’t be used. More often than not, manually configuring VPN connections or accessing them will take too much time and annoy the user. Forcing them to use it for specific applications might not work either, for the reasons that follow, as well as the fact that if they can get around VPN and still get the job done, they’ll go around it.
Other changes due to the lawsuit include: Organizations using wildcard entries for their VPN configurations (e.g., *.com) will not trigger an automatic VPN connection anymore, as the TLD is publically available.
Wildcard settings like this are used to establish VPN each time a user accesses the Internet to establish a link to corporate protection layers. With no VPN connection established, things like server-based DLP and content filtering are no longer going to protect those devices.
Apple also says that if the host is a webserver that presents different content to internal and external users, the previously established VPN rules for the network will stop working, thus the corporate user will be presented with external content only. This change can impact the use of tools such as ActiveSync or OWA with Exchange. Where those tools could be securely accessed via public domains (as long as the user had access to VPN) before, Apple’s changes will stop this practice.
So, if you wanted to send all traffic over a VPN connection to a centralized server for DLP or filtering, application access, or storage – what was once easy is now harder if not impossible without serious infrastructure changes. The problems caused by this change can be fixed and mitigated, but it will be costly to some organizations, and time consuming for many others. Some smaller organizations may not be impacted at all, and they’re the lucky ones.
“The impact of Apple’s announced changes to the VPN security within iOS underscores the substantial risks that organization’s face on a daily basis. The reliance on mobile devices and the manufacturers of operating systems to maintain security and integral features of a rapidly changing global economy is a huge risk for any organization,” commented MDM vendor Mobile Active Defense, in a whitepaper (PDF) on the impending changes.
“As vendors like Apple implement changes in their OS’s, which can dramatically impact the integrity of the underlying security of this powerful mobile ecosystem – it is incumbent upon security solution providers to be ready to rapidly assess and assimilate these changes, in order to advise customers and the industry at large about their potential impact,” the white paper added.
OpenDNS said that it is working on solutions for its Umbrella security product for iOS in order to address the changes coming from Apple later this month.
“We are both closely tracking the issue and aggressively pursuing alternative solutions. Although Apple has not shared a specific timeline for the feature release, our goal is to ensure that secure connectivity for your iOS devices can be maintained even after this update is deployed,” David Thompson, Senior Product Manager at OpenDNS explained in an email.
A Fortinet spokesperson told SecurityWeek that its iOS app does not rely on the affected API.
When asked for comment, Cisco declined to do so, as did several other vendors that have customers impacted (or potentially impacted as the case may be) by these changes. The lack of commentary is puzzling, but we’ll leave opinions off the table.
The support document from Apple is available here, but it is not clear as to when the update will be released, though some say it is likely to be very soon.
Additional reporting by Mike Lennon














