In some ways, an attack against an organization is similar to a house made of cards; removing one card can cause the whole thing to collapse.
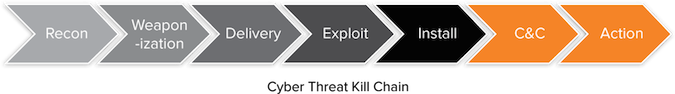
This concept can be applied to the cyber kill chain framework created by Lockheed Martin that describes the phases of an attack. Disrupting any of these stages can be enough to thwart, or at least slow, a hacker. While security experts have been talking about this for years, recent high-profile breaches have underscored the importance of thinking not just about preventing attacks, but also ways the damage attackers can do can be limited or caught when an attack is underway.
“Depending on their skill set, budget, and risk tolerance, each security team will take a different approach to the kill chain,” said Mark Nunnikhoven, Trend Micro’s vice president of cloud and emerging technologies.
“Some are great at minimizing their footprint which makes it hard for the attacker to weaponize what they’ve learned during reconnaissance,” he said. “Others are great a detection and focus on the catching the attacker during the exploit or install phases. Regardless of the approach, every security team is trying to make it so the attacker must spend more time and energy on the attack than the return they get.”
In a recently issued report, the security firm Aorato outlined what researchers believe are the various stages of the attack on Target. The firm notes the attackers’ main method of penetration was via stolen credentials as opposed to exploiting vulnerabilities, with the initial compromise being used to get access to a Target application for vendors. Then, the attackers exploited a vulnerability in the Web app and executed code on the application’s server.
From there, the report states, they searched for relevant targets to propagate to by querying Active Directory from the Web application’s server. The attackers then stole the access token of an account with Domain Admin privileges and used it to create a new Domain Admin account in Active Directory. Next they propagated through the network to relevant computers.
In the report, researchers noted the attackers used malware when no relevant legitimate tool existed that could be used for their purpose, such as for scraping the memory of the point-of-sale process. Rather than try to stay invisible using rootkits or other malware, the attackers relied on disguises – adding bogus user accounts, masking the malware files they did use with the names of legitimate files and using tools like Remote Desktop and PsExec to run processes on various machines remotely.
“Traditional security tools focus heavily on malware and miss these kinds of compromises,” said Chris Morales, practice manager of architecture and infrastructure at NSS Labs. “Companies need to provide continuous monitoring of internal systems looking for anything that is a deviation from normal system behavior. This means using a big data analytics system for analysis beyond a traditional SIEM as there is quite a bit of information to collect. Any abnormal behavior can be considered an indicator of interest and needs some level of investigation.”
The Target attackers used a staged approach to propagation, the report explains. First, they obtained a foothold on a new system through a manual connection (e.g. RDP) to assess its value. If they decided it was valuable, they upgraded their grip to a persistent one by adding a service to the target system backdoor or adding a backdoor.
In the case of retail breaches, the short-lived nature of attacks makes hiding in plain sight an attractive option for attackers, said Tal Be’ery, vice president of research for Aorato.
“For a short-lived campaign hiding in plain sight can be considered as a good enough camouflage from the attacker’s PoV [point of view], as the risk of detection is relatively small due to the current state of security measures and the relatively short campaign time,” he explained.
The Aorato report recommends organizations monitor and profile user access patterns, and utilize multi-factor authentication to protect sensitive systems. As an attacker’s first step begins with reconnaissance, the report also recommends keeping an eye out for signs of recon – with particular attention being paid to any change in LDAP queries. Other advice includes segregating networks, limiting user privileges and monitoring for the creation of new privileged user accounts.
When it comes to preventing data exfiltration, McAfee EMEA CTO Raj Samani said an organization’s firewall should monitor outgoing traffic against a list of known bad IPs, so that if a system internally is communicating with this system, it can be identified as an indication of compromise. Beyond this, organizations should also consider some form of network-based data loss prevention that will analyze outgoing traffic to determine whether it is indeed authorized to leave the environment, he said.
“The problem with disrupting the kill chain is that while it may eliminate the discovered breach, you don’t know where else a problem exists,” Morales said. “It needs to be done, but not in a manner obvious to the attacker. It might alert the attacker their presence is known allowing them to modify an ongoing attack for further evasion. The trick is to constrain the ability of the attack to cause any damage transparently to provide time to learn about the attacker while also identifying any further infections.”
“I have spent up to two weeks doing this,” he added. “It involves putting the infected systems into a sandbox where nothing gets hurt and more data can be collected. This should gather enough intel to identify all infected hosts and applications using some form of internal analysis tools.
In the end, the earlier an organization can disrupt the kill chain, the better.
“Since APT style attacks generally follow the stages of the kill chain, understanding and identifying these phases can help you to predict the attacker’s next move and put effective defenses in place,” said Lauren Barraco, product manager of AlienVault.”
*This story was updated to mention Lockheed Martin developed the Cyber Kill Chain framework.