“Luckycat” Attacks Targeting Defense Industry and Tibetan Activists Linked to Individual in China
Researchers at Trend Micro pulled the covers away from an attack campaign whose targets range from Tibetan activists to military research, aerospace and energy companies in India and Japan.
In a paper released Thursday, Trend Micro linked what it calls the “Luckycat” campaign to a series of attacks emanating from China. In a follow-up investigation, the New York Times identified a former Chinese graduate student named Gu Kaiyuan, who reportedly now works at Tencent, a Chinese technology company.
 According to Trend Micro, Luckycat was first thought to be targeting only military research organizations in India. However, it was also linked to attacks against aerospace, energy and other institutions in Japan. Since June 2011, it has been linked to at least 90 attacks, Trend Micro said.
According to Trend Micro, Luckycat was first thought to be targeting only military research organizations in India. However, it was also linked to attacks against aerospace, energy and other institutions in Japan. Since June 2011, it has been linked to at least 90 attacks, Trend Micro said.
“The Luckycat campaign attacked a diverse set of targets using a variety of malware, some of which have been linked to other cyber-espionage campaigns,” according to the report. “The attackers behind this campaign maintain a diverse set of C&C infrastructure and leverages anonymity tools to obfuscate their operations. We were able to track elements of this campaign to hackers based in China.”
Trend Micro identified five different malware families used by or hosted on the dedicated server used in the attacks. The campaign uses free web-hosting services that provide various domain names and IP addresses to make the operation more difficult to track, the researchers contended. The attackers also utilized virtual private servers that housed their primary piece of malware – TROJ_WIMMIE – as well as others in a bid to protect their campaign from being disrupted if the servers on the free hosting services were shut down for malicious activity.
“Using open source research, we were able to connect the email address used to register one of the Luckycat C&C servers to a hacker in the Chinese underground community,” the report states. “He uses the nickname, “dang0102,” and has published posts in the famous hacker forum, XFocus, as well as recruited others to join a research project on network attack and defense at the Information Security Institute of the Sichuan University. The hacker, also known as “scuhkr,” has authored articles related to backdoors and shellcode in a hacking magazine.”
The New York Times reported it was able to trace the name “scuhkr” to Gu Kaiyuan, a former graduate student at Sichuan University, in Chengdu, China. Contacted by the Times, Gu Kaiyuan declined to comment.
According to Trend Micro, the malware identified with the ShadowNet, Duojeen, Sparksrv, and Comfoo campaigns were used or found hosted on the same dedicated server used by the Luckycat campaign, indicating a possible connection between this attack campaign and the others.
“Targeted attacks are not isolated smash-and-grab incidents,” the report states. “They are part of consistent campaigns that aim to establish persistent, covert presence in a target’s network so that information can be extracted as needed.”
Sufficiently motivated threat actors can penetrate networks despite advanced security, blogged Nart Villeneuve, senior threat researcher at Trend Micro. Apart from standard attack prevention tools, enterprises should also focus on detecting and mitigating attacks and employing data-centric strategies, he wrote.
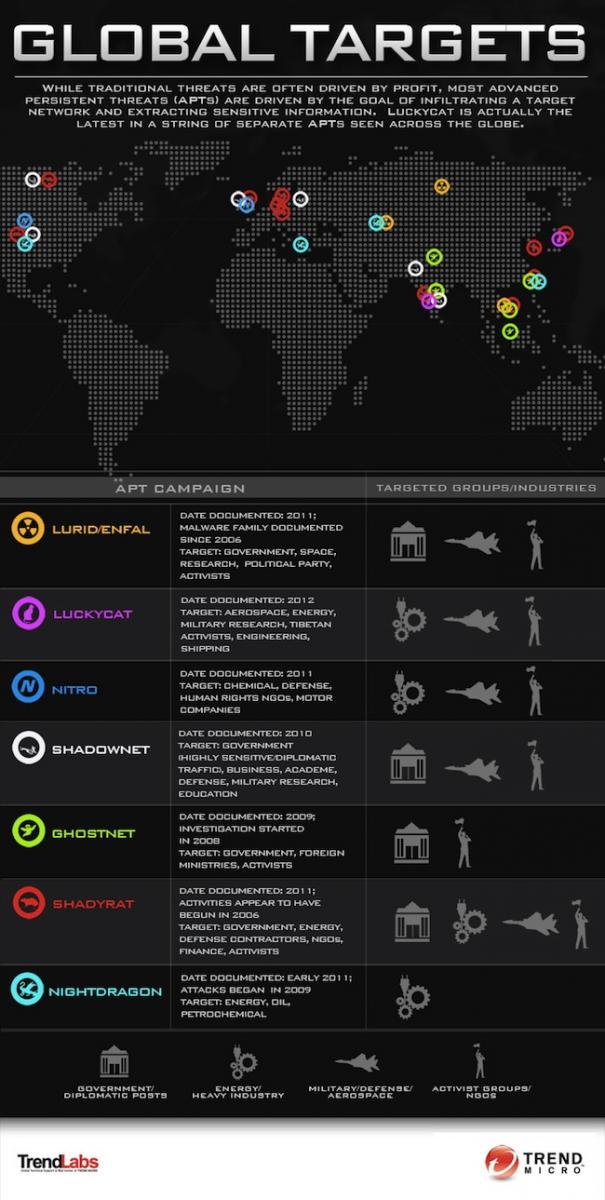
The full report from Trend Micro, “Inside an APT Campaign with Multiple Targets in India and Japan”, is available here. In order to help show how Luckycat measures up to other well-known threats, Trend Micro also created the infographic below.