In 1969, Apollo 11 landed men on the moon, marking the first time in human history that people walked on a surface other than Planet Earth. Five more manned moon landings happened during the next three years, and one could have assumed that this was just the first stage of interplanetary human expansion.
Except the expansion got interrupted by another, unplanned, humanity-wide project; the Internet. Since 1969, when two computers were first networked, we’ve been busily turning inward; creating networks that let people all around the globe talk to each other. And no one has been back to the moon since 1972. The Internet interrupted space colonization.
Interrupting the Interruption
The Internet of Things (where non-humans are the clients as well as the servers) is now on the verge of interrupting the Internet. Like the original Internet, the Internet of Things has grown somewhat organically with apparently very little consideration for security.
We have an opportunity to learn from the mistakes of the original Internet and build some security into the Internet of Things, if we act quickly.
One of the lessons that we can apply immediately is the concept of threat modeling. Threat modeling is a process fundamental to the Software Development Lifecycle (SDLC), but it is a broad process that actually doesn’t have to be specific to software at all.
This article marks the start of a series on how to threat-model the Internet of Things. In this series, we’ll look at the new threat surfaces presented by “things as clients” and the risks of increasing the number of endpoints on the Internet by orders of magnitude very quickly.
It’s Not Just Internet-connected Toasters
Don’t dismiss the IoT as just a consumer security problem. IoT security is critical for other sectors beyond retail. Consider:
Government: City planners are busily designing so-called smart cities replete with sensors and connectors to make services more efficient. IoT can optimize ground transportation, shipping and power for smart cities, and all of these services will be using the IoT.
Industrial: Heavy industries will monitor workers’ exposure to dangerous natural or synthetic chemicals with internet-connected sensor networks. Sensors in factories will assist with predictive maintenance and feed operational data into analytic engines. General Electric jet engines already produce terabits of data that airlines use to optimize flight paths and fuel plans.
Enterprise: The new world of soft perimeters will be complicated by the IoT. Nearly half of all new tech workers are remote employees who often work from their domiciles. Imagine their houses full of hundreds of quasi-secure IoT devices hoping to catch a ride into the corporate VPN. IT departments are already sweeping their guest networks for the rogue IoT devices appearing there.
Each of these groups (consumer, government, industrial, and enterprise) will be affected and, in some cases, transformed by IoT. Threat modeling the IoT can translate the context of each of these groups into better security for the IoT as a whole, as we’ll see in this series.
Let’s Fix IoT Now Before We Go Back to Space
Like the original Internet, the IoT might revolutionize everything. Unlike with the original Internet, we have an awareness about security and the opportunity to build security into the Internet of Things.
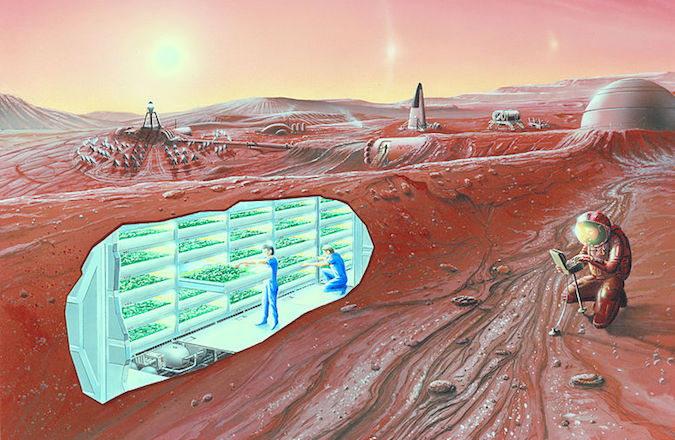
Image Attribution: By NASA Ames Research Center – NASA Ames featured images, Public Domain
The 1969 project of space exploration is seeing renewed interest with Elon Musk’s SpaceX and Mars colonization project. So those who were excited about space in 1969 can rejoice that while we might have taken a half-century hiatus, we might be getting back space exploration back on track.
It would a pretty good idea to make sure we can secure our undoubtedly-internet-connected spaceships before we leave, wouldn’t it?
Now that we’ve set the stage, the next piece in this series looks closer at the threat modeling process and begin defining the security scope of the Internet of Things.
















