Defense.Net Launches New DDoS Mitigation Service
Defense.Net, a startup dedicated to combating Distributed Denial of Service (DDoS) attacks, this week launched DDoS Frontline, a new mitigation service designed to help customers fend off powerful and always-changing DDoS attacks.
As a startup, Defense.Net is entering into an increasingly crowded and competitive space, but believes its technology and platform differentiates from many DDoS mitigation solutions currently on the market.
The company was was founded by Barrett Lyon, an early pioneer in DDoS mitigation more than 10 years as founder of Prolexic, a DDoS protection firm recently acquired by Akamai Technologies for $370 million in cash.
DDoS Frontline protects against a wide range of DDoS attack types, from low-level Layer 7 attacks to the increasingly frequent large-scale attacks, the company said.
“The DDoS threat is constantly morphing and requires that businesses have the most current defenses in place,” said Lyon, who serves as the company’s CTO.
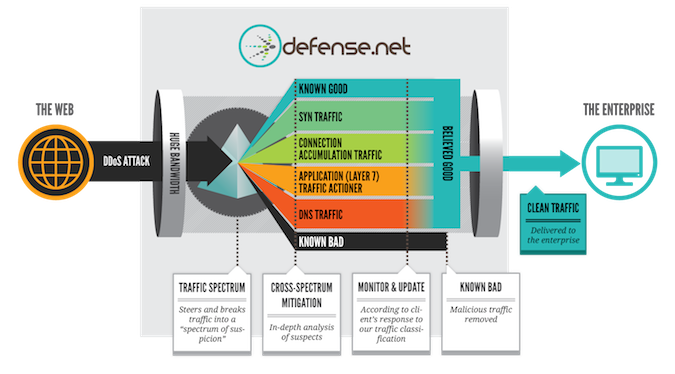
When deployed, Defense.Net’s mitigation technology intercepts each packet of traffic to determine its legitimacy and automatically route it to the most appropriate of Defense.Net’s different mitigation solutions.
“It breaks down multi-layer attacks into their components for more thorough mitigation via the only systems specifically designed to mitigate each attack vector, versus legacy DDoS solutions that have a ‘one box does all’ approach,” the company explained.
While most DDoS attacks have traditionally targeted Web sites, attackers are increasingly attacking non-Web based protocols that power key applications and services residing in datacenters, such as NTP,TELNET, FTP, SNMP, SMTP, POP-3, CHARGEN, MIME and DNS. Defense.Net’s DDoS Frontline helps protect those services.
Frontline also includes Defense.Net AttackView, an interactive customer portal that provides detailed information on attacks in real-time, as well as post-attack analysis.
“AttackView breaks down each attack into a unique timeline ‘story’ and contains information on attack type, source and size and also the mitigation techniques utilized,” the company said. It also includes data such as attack origin, diagnostics of the attack traffic, specific mitigations performed, the result of each mitigation vector on attack traffic, and how each attack responds and morphs based on the specific mitigations performed.
Defense.Net’s DDoS Frontline service is backed by what the company calls its “Zero Day Team”, a group of DDoS mitigation experts and network operators put in place to provide enterprises with high levels of transparency, and to support customers.
“DDoS attacks have grown significantly in the past 18 months, taking down even some of the largest and most heavily defended websites,” said Chris Risley, CEO of Defense.Net. “DDoS Frontline offers an entirely new set of network technologies specifically designed to protect large enterprises and critical infrastructure from today’s DDoS attacks and the growing number of actors carrying out these attacks.”
The company has raised more than $9.5M in debt and equity financing with investors that include Bessemer Venture Partners.















