Security firm Imperva has analyzed web application vulnerability trends in 2016 and determined that while some types of flaws have declined, others have become more common.
Data collected by the company shows that the total number of vulnerabilities found over the past two years has increased, but the number of flaws affecting web applications has actually dropped.
Imperva believes this trend can be attributed to a shift in research focus (e.g. towards IoT devices), and is likely not caused by web applications being more secure than before. Furthermore, the company pointed out that its data sources don’t cover vulnerabilities in proprietary web application code.
More than a quarter of the flaws tracked by the company have been classified as high priority, indicating that they pose a serious risk to affected systems.
When it comes to vulnerabilities by attack type, Imperva has observed a significant increase in denial-of-service (DoS) bugs, but the rate of cross-site scripting (XSS) issues has declined over the past year. Buffer overflows also increased slightly in 2016, but directory traversals, remote file inclusion, cross-site request forgery (CSRF) and SQL injections remained at roughly the same levels.
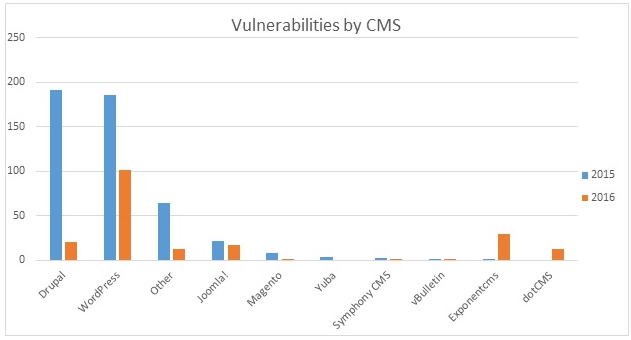
As for vulnerabilities related to content management systems (CMS), the number of issues affecting Drupal and WordPress dropped significantly in 2016 compared to the previous year, but the number of flaws identified in less popular products, such as Exponent and dotCMS, has increased.
Experts believe CMSs with a smaller market share might have a larger proportion of flaws as a result of fewer resources and less investment in security.
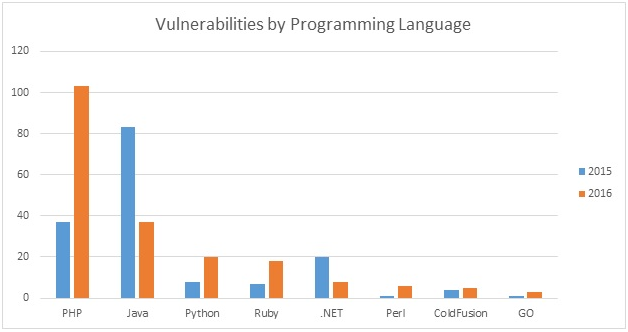
Imperva has found that the number of vulnerabilities affecting programming languages such as PHP, Python, Ruby, Perl, ColdFusion and Go has increased in 2016 compared to 2015. PHP takes the lead in this category with a growth of more than 100 percent. The security firm believes this can be attributed to the release of a new PHP version in December 2015.
Related: Brute Force Attacks on WordPress Websites Soar
Related: Over 8,800 WordPress Plugins Have Flaws, Study Shows












