The personal details of millions of Verizon customers were exposed online due to a misconfigured Amazon Web Services (AWS) S3 bucket operated by a third-party vendor, but the telecoms giant has downplayed the incident.
Cyber resilience firm UpGuard reported on Wednesday that its researchers discovered an unprotected AWS S3 bucket containing information on as many as 14 million Verizon customers, including names, addresses, phone numbers, PINs used for identity verification purposes, customer satisfaction data, and service purchases.
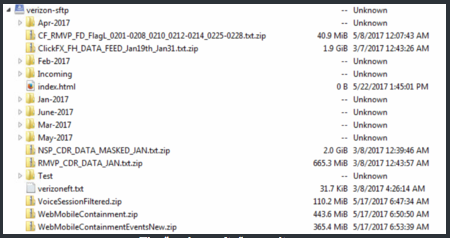
The data, which appears to represent daily logs collected over the first six months of 2017, was not exposed by Verizon itself, but by NICE Systems, an Israel-based partner that provides call center services. UpGuard reported the leak to Verizon on June 13, but the exposed database was only protected on June 22.
“Beyond the sensitive details of customer names, addresses, and phone numbers—all of use to scammers and direct marketers—the prospect of such information being used in combination with internal Verizon account PINs to takeover customer accounts is hardly implausible. To do so would enable impersonators to tell Verizon call center operators to do whatever was wished of them,” UpGuard said in a blog post.
In a statement published on its corporate website, Verizon downplayed the incident, claiming that the details of only 6 million unique customers were exposed. The company blamed the leak on human error, and pointed out that no one other than UpGuard had accessed the unprotected cloud storage area.
“The overwhelming majority of information in the data set had no external value, although there was a limited amount of personal information included, and in particular, there were no Social Security numbers or Verizon voice recordings in the cloud storage area,” Verizon said.
“To further clarify, the data supports a wireline portal and only includes a limited number of cell phone numbers for customer contact purposes. In addition, to the extent PINs were included in the data set, the PINs are used to authenticate a customer calling our wireline call center, but do not provide online access to customer accounts,” the company added.
Experts believe this is a serious incident, even if no one else downloaded the data from the cloud storage.
“Sure, a mid-air miss is better than an air flight disaster, but neither should ever happen,” John Gunn, chief marketing office for VASCO Data Security, told SecurityWeek. “Data such as this can be used by hackers for all types of attacks, especially phishing attacks, by giving them legitimacy in the mind of the victim. We saw this recently with the DocuSign breach and the subsequent successful attacks against their users.”
Willy Leichter, vice president of marketing at Virsec, believes “this will be a heated board-level issue for a $1 billion company like Nice, and a $125 billion-plus company like Verizon.”
“If the European General Data Protection Regulation (GDPR) was in effect (it is starting in May 2018) there could be a fine as large at $5 billion (4% of annual revenue) for this single incident,” Leichter said.
Related: U.S. Defense Contractor Exposes Sensitive Military Data
Related: Republican Party Contractor Exposes Details of 198 Million American Voters














