Non-destructive Cyber Attack Could be Considered a Warning to North Korean Regime
The United States Cyber Command has reportedly been engaged in offensive activity, namely a DDoS attack, against North Korea’s military spy agency, the Reconnaissance General Bureau (RGB). The attack is thought to have commenced on September 22, and continued until September 30.
The attack occurred just five weeks after President Trump elevated U.S. Cyber Command to a Unified Combatant Command. At the time, Trump said, “The elevation of United States Cyber Command demonstrates our increased resolve against cyberspace threats and will help reassure our allies and partners and deter our adversaries. Through United States Cyber Command, we will tackle our cyberspace challenges in coordination with like-minded allies and partners as we strive to respond rapidly to evolving cyberspace security threats and opportunities globally.”
 The few details currently available on this DDoS attack come from a Washington Post report published Saturday. The report says that the Reconnaissance General Bureau was targeted, “by barraging their computer servers with traffic that choked off Internet access.” The effects were temporary and non-destructive. “Nonetheless, some North Korean hackers griped that lack of access to the Internet was interfering with their work, according to another [anonymous] U.S. official.”
The few details currently available on this DDoS attack come from a Washington Post report published Saturday. The report says that the Reconnaissance General Bureau was targeted, “by barraging their computer servers with traffic that choked off Internet access.” The effects were temporary and non-destructive. “Nonetheless, some North Korean hackers griped that lack of access to the Internet was interfering with their work, according to another [anonymous] U.S. official.”
The action seems to be partly in response to North Korean cyberattacks, and partly an aspect of a wide-ranging diplomatic offensive led by Secretary of State Rex Tillerson, who was in Beijing on Saturday. “What I can tell you,” said a senior administration official to the Washington Post, “is that North Korea has itself been guilty of cyberattacks, and we are going to take appropriate measures to defend our networks and systems.”
That this cyber attack was non-destructive and temporary suggests it could be considered more as a warning than a punishment. It is Cyber Command telling North Korea that it has its range and is capable of much stronger action. By being non-destructive it is probably hoped that it won’t provoke kinetic retaliation; although it is quite likely to provoke cyber retaliation from North Korean hacking groups.
In July 2017, researchers from Recorded Future monitored internet traffic from North Korea. One of its conclusions was that “most state-sponsored activity is perpetrated from abroad.” Recorded Future suggested that North Korean malicious activity most like originates from countries such as India, Malaysia, New Zealand, Nepal, Kenya, Mozambique, and Indonesia. Under these circumstances, it is unlikely that DDoSing the homeland would have much effect on the actual hackers; although it would disrupt coordinating control from the RGB.
“DDoSing the Reconnaissance General Bureau might not affect the hackers outside of North Korea directly,” F-Secure’s security adviser Sean Sullivan told SecurityWeek, “but it could possibly hamper communications, forcing them to use other (potentially monitored?) channels.”
His colleague, Tom Van de Wiele, agreed and added, “Or as an extra bonus, to see what procedures they would go for versus what kind of panicky moves the organization makes, that [Cyber Command] could later abuse, monitor or exploit.” The suggestion here is that it wasn’t just a warning shot to North Korea, but an elaborate cyber reconnaissance project.
One thing not yet known is whether China had any involvement or collusion in the action. Since Tillerson was in Beijing at the time, and since all internet traffic into and out of North Korea is through China via a China Unicom link operating since 2010, it is a tempting thought. Either way, however, this potential choke point against North Korean cyber access is in the process of weakening.
Russia, on Sunday, started providing a second internet route for North Korea. The link started showing on Dyn Research peer observance tables at around 0900 UTC on October 1. Connectivity was clearly unstable for about three hours, but stabilized after that. In effect, it went live with a stable link between Russia and North Korea shortly after the U.S. Cyber Command action finished.
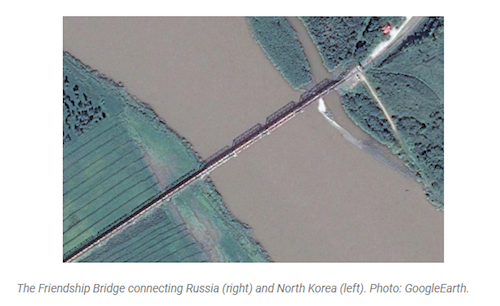
The route is supplied by Russian telecommunications company TransTeleCom. TransTeleCom is a subsidiary of the Russian railway operator, and lays its fiber optic lines alongside the railway tracks. A map on the company website shows a cable running to the North Korean border. It is assumed that this cable now connects Russia and North Korea via the Friendship Bridge across the Tumen River — the only point at which the two countries connect.
The cabling has apparently been in place under an agreement between TransTeleCom and Korea Posts and Telecommunications Corp since 2009. The timing coincidence of it becoming live now could imply that opening the link between the two countries is in response to the U.S. Cyber Command attack. Alternatively, it could lend weight to the F-Secure hypothesis. If Cyber Command was aware that this would be happening, the DDoS attack could have been an attempt to provoke the Reconnaissance General Bureau into revealing channels to its overseas hacking groups prior to the Russian link giving North Korea additional communications options.














