South Korea’s Internet & Security Agency (KISA) has issued an alert for a zero-day vulnerability in Flash Player that has reportedly been exploited in attacks by North Korean hackers.
Few details have been provided, but KISA says the vulnerability affects Flash Player 28.0.0.137 and earlier. Version 28.0.0.137 is the latest, released by Adobe in January as part of the Patch Tuesday updates.
The security hole can be exploited by getting a user to open a document, web page or email containing a specially crafted Flash file, KISA said on Wednesday.
Simon Choi of South Korea-based cybersecurity firm Hauri said on Twitter the Flash Player zero-day has been exploited by North Korea since mid-November 2017 in attacks aimed at South Korean individuals who focus on researching North Korea.
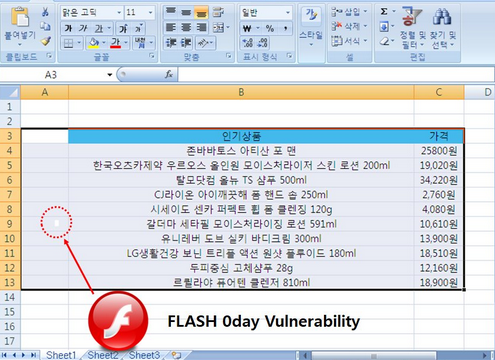
According to the expert, the flaw has been leveraged to distribute malware. A screenshot he posted appears to show that the exploit has been delivered via malicious Microsoft Excel files.
SecurityWeek has reached out to Adobe for comment and will update this article once the company responds. Since the activities of North Korean threat actors have been closely monitored by several security firms, it’s possible that Adobe has already been made aware of the zero-day and is working on a patch.
UPDATE. Adobe says it’s aware of a report that an exploit for a vulnerability it tracks as CVE-2018-4878 exists in the wild, and is being used in limited, targeted attacks against Windows users. The company says it will address the flaw with an update planned for the week of February 5.
In an advisory, Adobe said the vulnerability is a critical use-after-free that allows remote code execution. Until a patch becomes available, the company has provided some mitigations.
“Beginning with Flash Player 27, administrators have the ability to change Flash Player’s behavior when running on Internet Explorer on Windows 7 and below by prompting the user before playing SWF content,” Adobe said. “Administrators may also consider implementing Protected View for Office. Protected View opens a file marked as potentially unsafe in Read-only mode.”
Related: Middle East Group Uses Flash Zero-Day to Deliver Spyware
Related: APT Group Uses Flash Zero-Day to Attack High-Profile Targets
Related: Adobe Patches Flash Zero-Day Exploited by APT Group












