OpenDNS has released a tool along with its source code, that enables encrypted DNS traffic, much in the same way SSL enables encrypted HTTP traffic.
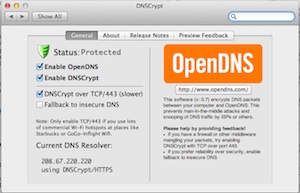
According to OpenDNS, and any researcher or vendor who has ever worked in the field, some of the underlying foundations of the DNS protocol are inherently weak, especially what they call the “last mile” – or the part of the internet connection between the client and the ISP. To address this, OpenDNS released a preview of DNSCrypt.
“DNSCrypt is a slight variation on DNSCurve,” the tool’s documentation explains.
“DNSCurve improves the confidentiality and integrity of DNS requests using high-speed high-security elliptic-curve cryptography. Best of all, DNSCurve has very low overhead and adds virtually no latency to queries. DNSCurve aims at securing the entire chain down to authoritative servers. However, it only works with authoritative servers that explicitly support the protocol. And unfortunately, DNSCurve hasn’t received much adoption yet.”
The DNSCrypt protocol is very similar to DNSCurve, in that they both use elliptic curve cryptography, but DNSCrypt focuses on securing communications between a client and its first-level resolver, otherwise known as the aforementioned last mile.
“While not providing end-to-end security, it protects the local network (which is often the weakest link in the chain) against man-in-the-middle attacks. It also provides some confidentiality to DNS queries,” the documentation added. For more details on the DNSCurve and Curve25519, head here.
In the meantime, DNSCrypt will stop DNS replay, observation, and timing attacks, as well as Man-in-the-Middle attacks and resolver impersonation attacks. The tool, available already compiled for OS X, will also run on OpenBSD, NetBSD, Dragonfly BSD, FreeBSD, and Linux. There is no Windows client, which is odd considering a majority of the 30 million OpenDNS users run Microsoft’s operating system. OpenDNS made no mention of when a Windows version is to be expected.
“DNSCrypt is a critical advancement for the DNS, for global Internet security efforts and for the Internet at large,” said OpenDNS CEO David Ulevitch.
“The technology empowers Internet users to secure their own Internet and DNS use and protect themselves from nefarious activity that happens through their DNS connection, but also to insulate themselves from their Internet Service Provider’s uninhibited access to their DNS activity and domain lookup history. All Internet users have a right to privacy and DNSCrypt gives them both that and a heightened level of security.”
Related Reading: The Top Five Worst DNS Security Incidents
Related Reading: Trouble Ahead – The Implementation Challenges for DNSSEC
Related Reading: Deploying DNSSEC – Four Ways to Prepare Your Enterprise for DNSSEC
Related Reading: Five Strategies for Flawless DNSSEC Key Management and Rollover
Related Reading: The Missing Ingredients for DNSSEC Success
Related Reading: Do Recent BGP Anomalies Shed a Light on What’s to Come?














