After security researchers from FireEye said they identified a PDF zero-day that was being used in targeted attacks, Adobe late Wednesday confirmed the existence of two critical vulnerabilities in Adobe Reader and Acrobat XI for Windows and Macintosh that are being exploited in active attacks.
Shortly after Adobe’s acknowledgement of the vulnerabilities, at approximately 11:30PM ET Wednesday night, FireEye shared additional details on the attack.
As background, the exploits have been seen in extremely targeted attacks against high profile targets, and are a sophisticated effort that appear to be the first to successfully escape Adobe’s “protected mode” sandbox.
The two vulnerabilities were assigned CVE’s CVE-2013-0640 and CVE-2013-0641.
“[The attack] is very sophisticated and leveraged a few advanced exploitation techniques,” Zheng Bu, senior director of security research at FireEye, told SecurityWeek.
FireEye did not share the target of the attack which led to its discovery.
Not surprisingly, the attackers were executing the attacks by using a malicious PDF file delivered via a spear-phishing email that was designed to trick Windows users into clicking on it and triggering the exploit.
Speaking with ThreatPost on Wednedsay morning, Bu said the exploit purports to be a Visa application for a non-English speaking country. Patterns in the malware originally led researchers to believe the attacker may have a Latin or Spanish-speaking background, but FireEye later concluded that it was Italnian. A source familiar with the malware told SecurityWeek the malicious file used was a Visa form for the country of Turkey.
What’s interesting about this attack, is that the embedded JavaScript code attempts to determine the version of Adobe Reader being used and generate the appropriate shellcode based on what version was found.
“The JavaScript embedded in the crafted PDF is highly obfuscated using string manipulation techniques. Most of the variables in the JavaScript are in Italian,” FireEye reseachers noted in a blog post. “The JavaScript has version checks for various versions of Adobe Reader as shown below and it creates the appropriate shellcode based on the version found.”
In order to bypass ASLR (Address space layout randomization) and DEP (Data Execution Prevention), the shellcode is in a format of ROP chain, and will create a new DLL file on the disk and execute it by calling LoadLibraryA(), FireEye researchers said.
After loading the malicious library, the malware enters a long sleep but eventually will load the payload.
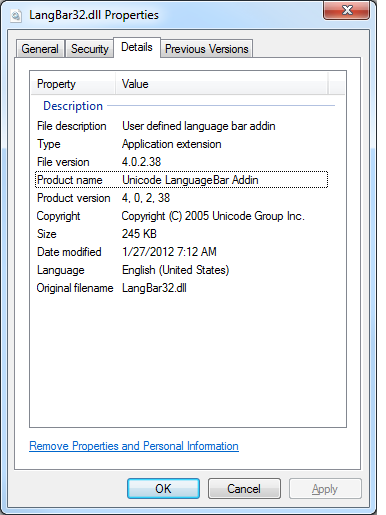
“The payload involved in this exploit ultimately installs what appears to be a first stage downloader in the form of a DLL posing as a “language bar addin,” using the registry key “HKCUSoftwareMicrosoftCTFLangBarAddIn” to persist after reboot,” FireEye explained. “It further attempts to legitimize this disguise in its file properties.”
Roel Schouwenberg, a senior security researcher at Kaspersky Lab, told the company’s news service that they can confirm the malicious PDF’s ability to escape the Reader sandbox.
“We can confirm the existence of a malicious PDF in the wild that’s successfully able to break out of Adobe Reader’s sandbox,” Schouwenberg told ThreatPost on Wednesday. “We’ve seen successful exploitation on a machine running Windows 7×64 and Adobe Reader 11.0.1.”
Evasion
In order to evade detection and analysis, the malware checks which process it is loaded into against a list of processes that would normally consider loading a language bar and refrains from certain behaviors if there is no match, FireEye said.
It also uses a TLS callback function to start a thread before the entry point is reached, and populates its export table with more than 200 fake entries. The fake entries, FireEye said, are named after Windows Property System functions but point to invalid memory locations.
“The latter is particularly effective at muddying up sandbox analysis reports that enumerate exports in a DLL and attempt to call each of them,” FireEye explained.
After an initial GET request, the malware also makes various POSTS. “In response to the POST we observed additional payloads being downloaded. The two of note are libarext32.dll and libarhlp32.dll which it downloads and loads. It also creates a data file called “kmt32.pod”. It is unclear what the contents of this file are so far,” the researchers said.
The command and control server appears to be hard-coded (fixed) and is hosted at a European web hosting provider, Bu told SecurityWeek.
Update: As of Thursday morning, mutiple sources have comfirmed with SecurityWeek that the C&C server connected to this particular campaign has been taken offline. However, given that the vulnerability remains unpatched and the exploits still work, creating a new attack using the same exploits but a different C&C server is trivial for attackers.
The compile times for five different payloads are very recent and range from Jan. 24, 2013 to Feb. 4, 2013.
 FireEye also said the malware has the capability built in to uninstall itself under certain conditions, or enter into a long term sleep mode.
FireEye also said the malware has the capability built in to uninstall itself under certain conditions, or enter into a long term sleep mode.
Finally, FireEye noted that the author used “666C” as the preferred Image Base, something the researchers believe is in reference to the verse from Revelation in the bible from which heavy metal band “Iron Maiden” drew inspiration for their album and song “The Number of the Beast”. FireEye has named the malware “Trojan.666” based on that discovery.
Both FireEye and Adobe have held back from sharing additional technical details on vulnerabilities in the interest of preventing exploit writers from being better informed about the vulnerability.
If additional technical details were leaked, exploit writers and crimekit developers would be likely have the exploits implemented in short time and ready to attack the masses.
Mitigation and Defense
While waiting for a patch, users of Reader XI and Acrobat XI for Windows can protect themselves from the exploit by enabling Protected View, Adobe said.
On Windows, Protected View (PV) is designed to be a highly secure, read-only mode that blocks most actions and application behavior until the user determines whether or not to trust the document.
“Under the covers, the PV sandbox is similar to Reader’s Protected Mode sandbox and provides equal protection,” Adobe explains. “Just like Reader, Acrobat strictly confines the execution environment of untrusted programs; that is, any PDF and the processes it invokes. When PV is enabled, Acrobat assumes some or all PDFs are potentially malicious based on user preferences and confines processing to a restricted sandbox.”
To enable the Protected View setting, choose the “Files from potentially unsafe locations” option under the Edit > Preferences > Security (Enhanced) menu.
Enterprise administrators can protect Windows users across their organization by enabling Protected View in the registry and propagating that setting via GPO or any other method, Adobe said.
Additional details on enabling Protected View for the enterprise are available here.
When Will Adobe Issue a Patch?
Adobe said that it is currently in the process of developing a fix for the vulnerabilities. Given the severity of the vulnerabilities, it’s likely that Adobe will rush a patch as soon as possible, but a release date for a fix has not yet been set.
According to Adobe, the affected software versions are:
· Adobe Reader XI (11.0.01 and earlier) for Windows and Macintosh
· Adobe Reader X (10.1.5 and earlier) for Windows and Macintosh
· Adobe Reader 9.5.3 and earlier 9.x versions for Windows and Macintosh
· Adobe Acrobat XI (11.0.01 and earlier) for Windows and Macintosh
· Adobe Acrobat X (10.1.5 and earlier) for Windows and Macintosh
· Adobe Acrobat 9.5.3 and earlier 9.x versions for Windows and Macintosh
Ironically, just last week at the Kaspersky Lab Security Analyst Summit in Puerto Rico, David Lenoe, Adobe’s Product Security Incident Response Team group manager, said that up until then, Adobe had not seen any exploit successfully bypass the sandbox in Reader and Acrobat.
Lenoe also shared some interesting stories and outlined some of the challenges vendors face with dealing vulnerability reports, especially when there is only “partial disclosure”.
This is a developing story and much more analysis and information is expected to come from FireEye, Kaspersky Lab and several other security vendors. Now that an advisory has been issued by Adobe, the company will likely remain quiet on the issue until a patch is ready or close to ready.














