This time every year I tell myself the same thing: “You’ve got to cut back on the drinking.” But I’m not about to listen to some weirdo who talks to himself. Yet, I want to make some kind of resolution! What’s left of the professional in me has some ideas about resolutions that we, as a security community, can make. Here are five.
1. Let’s get Santa milk and cookies and SSO in the cloud
The foundations have been laid for true single sign-on in the cloud with the fairly broad adoption of SAML federation. The 800-pound gorilla that is Office365 supports federation all the way back to your Active Directory server. So why not give all your employees single sign-on for Christmas? It’s the gift that will keep on giving for the rest of year. Don’t forget to enable Multi-Factor Authentication though, at least for the employees you actually care about, lest a Grinch get them.
2. Let’s split the risk
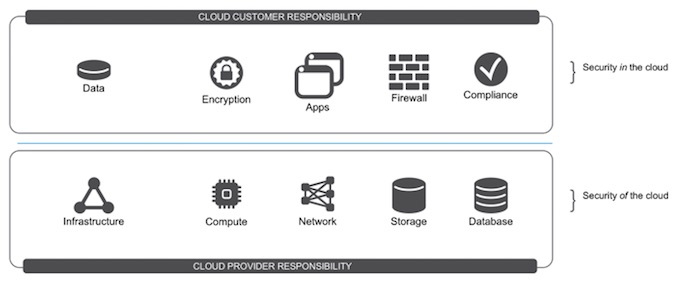
You know who’s in the cloud? Besides Santa? You are. When you moved your application to the cloud, you transferred some of the management of infrastructure security to the providers. But don’t forget, you’re still responsible for your application security and your data. Resolve to shift your InfoSec focus from network security to application security in response.
3. Let’s flatten the security speed bump
HTTP/2 and TLS1.3 are going to make the Internet faster. HTTP/2 is already multiplexing connections to reduce latency. TLS1.3, which should make it to draft status this year (how long have we been saying that, though?) will include modifications for zero-round-trip and single-round-trip data transmissions. Google has been using a modified form of this (called QUIC) on its servers for over a year. The rest of us can catch up with TLS1.3.
4. Let’s laugh more about consumer security
In 2016, attackers demonstrated what they were capable of doing with IoT devices and botnets like Mirai. Without regulations in place, consumer IoT device manufacturers will continue to lack any incentive to prioritize security in the year ahead. It would be nice if 2017 saw some kind of increase in consumer Internet security, but that’s probably just wishful thinking. In reality, snooping Barbies and malevolent toasters will be keeping us busy for years.
5. Let’s let go of the BYOD and watch for the APT
Ryan McGeehan wrote an excellent piece just in time for the new year. The whole article is instructive, but one point in particular deserves emphasis.
“[BYOD] does not well characterize the direct attacks happening against individuals within organizations.
This year’s incidents involving APT groups notably focused their attacks directly on employee’s personal emails and endpoints. Whether they show up at the office with their personal devices won’t matter if they’re sharing credentials or access tokens on personal accounts and devices, or accessing corporate accounts from home.”
BYOD as a threat vector is still a thing, but we need to realize that a truly targeted organization is going to have endpoints in their employees’ homes, and those endpoints may be getting attention from APT groups as well as Santa.
Resolutions
There’s a reason that resolutions happen around the New Year. It’s a time to reflect on (or shudder at) the previous year and resolve to do better next year. You’ll see a lot of security predictions coming around this time of year, and you can make your resolutions based on those. Or you can look back at your own year and customize your own security resolutions.
Personally, I’m going to resolve to drink less. Starting next year. Yeah. Next year.














