Exploitation attempts targeting a recently disclosed vulnerability affecting Zyxel firewalls started just one day after the flaw’s existence came to light.
Cybersecurity firm Rapid7 and Zyxel informed users on May 12 that Zyxel’s ATP, VPN and USG FLEX series business firewalls are affected by a critical vulnerability that can be exploited by a remote, unauthenticated attacker for arbitrary code execution as the “nobody” user.
The flaw, tracked as CVE-2022-30525, can be exploited through a device’s HTTP interface. Rapid7 has developed a Metasploit module and showed how an attacker could exploit the vulnerability to obtain a reverse shell.
The security hole was reported to Zyxel in April and it was quickly patched with the release of ZLD 5.30, but the vendor did not inform customers about the vulnerability and the associated risks until Rapid7 made its findings public on May 12 in an effort to help defenders detect potential exploitation.
The Shadowserver Foundation reported over the weekend that it had started seeing exploitation attempts targeting CVE-2022-30525 on May 13.
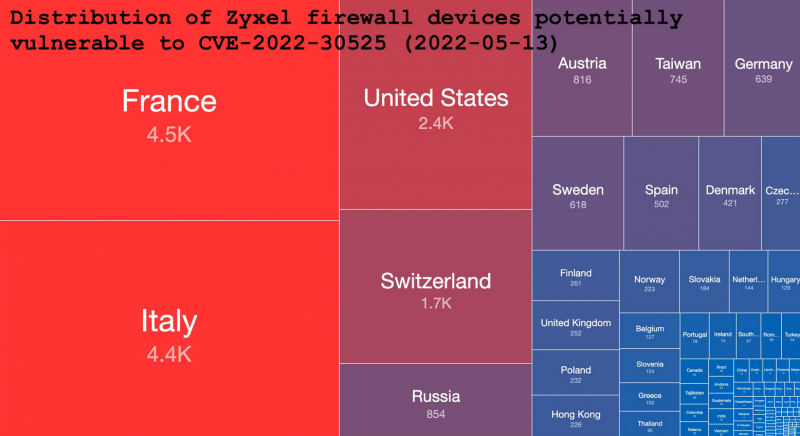
While Rapid7 saw roughly 15,000 potentially affected devices exposed to the internet, Shadowserver has identified nearly 21,000 possibly impacted firewalls, mostly located in France, Italy, the United States and Switzerland.
After seeing Shadowserver’s alert, NSA Cybersecurity Director Rob Joyce took to Twitter to warn organizations about the exploitation attempts and advised them to patch their firewalls. In response to Joyce’s tweet, threat intelligence company Bad Packets also reported detecting “events” related to CVE-2022-30525.
No information has been provided on the exploitation attempts, but most of them are likely part of internet scans whose goal is to identify vulnerable systems.
Proof-of-concept (PoC) exploits targeting the vulnerability have been made public, as well as open source tools for detecting exploitation attempts.
This is not the first time threat actors have targeted Zyxel firewalls in their operations.
Related: Over 20 Zyxel Firewalls Impacted by Recent Zero-Day Vulnerability
Related: Many Backdoors Found in Zyxel CloudCNM SecuManager Software
Related: Hardcoded Credentials Expose Zyxel Firewalls and WLAN Controllers to Remote Attacks
Related: Zyxel Patches Zero-Day Vulnerability in Network Storage Products














