Cybercriminals have been serving malicious advertisements on several high-profile websites in an effort to push shady software onto the computers of their visitors, regardless if they are Windows or OS X users, Cisco reported on Monday.
The company’s TALOS Security Research group has been monitoring this malvertising campaign since May, with the highest level of activity being recorded in mid-June and at the beginning of July. The operation has been dubbed “Kyle and Stan” because most domain names used for distributing malicious software contain the strings “kyle” or “stan” (possible inspired by two characters in the animated sitcom South Park).
According to Cisco, a large number of high-profile websites have served malicious advertisements from the Kyle and Stan network, including amazon.com, winrar.com, youtube.com and ads.yahoo.com. Researchers have identified more than 700 domains as part of this malvertising operation, but they believe the actual number is most likely much higher since the domains appear to be registered through an automated process.
During the course of its investigation, the company identified close to 10,000 connections to the malicious domains.
The attack itself is not different from other malvertising campaigns. The attackers have targeted a major online advertising company and they are abusing its systems to serve malicious ads to the visitors of high-profile websites. When users access the affected websites, they can be presented with a rogue ad which redirects them to another site depending on the user agent.
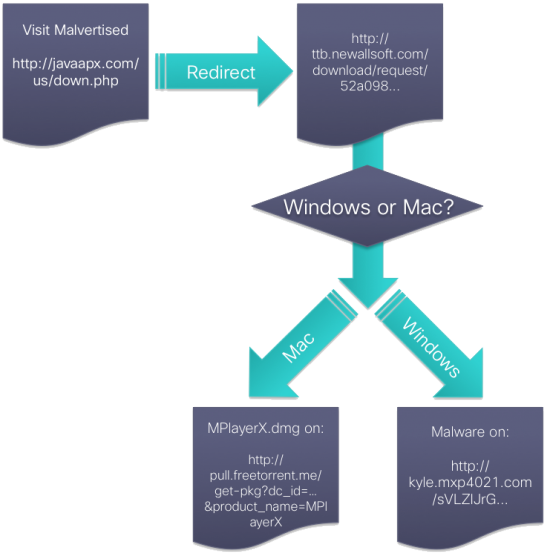
“Once the victim gets redirected to the final URL, the website automatically starts the download of a unique piece of malware for every user. The file is a bundle of legitimate software, like a media-player, and compiles malware and a unique-to-every-user configuration into the downloaded file,” Cisco Threat Researcher Armin Pelkmann explained in a blog post. “The attackers are purely relying on social engineering techniques, in order to get the user to install the software package. No drive-by exploits are being used thus far.”
When Mac users visit a website that displays a malicious ad, they’re taken to a page where they are served what appears to be a legitimate application called MPlayerX. However, the media player is bundled with VSearch and Conduit, a couple of pieces of adware that hijack victims’ browsers.
In the case of Windows users, they are served an adware/spyware dropper. While the instances analyzed by Cisco have involved only adware, spyware and browser hijackers, experts believe that other types of malware could also be distributed by the attackers.
“The malware droppers employ clever techniques and encryption to always have unique checksums to avoid detection,” Pelkmann said. “The large number of domains allows the attackers to use a certain domain just for a very short time, burn it and move on to use another one for future attacks. This helps avoiding reputation and blacklist based security solutions.”
Malvertising can be a very efficient method of spreading malware so cybercriminals are increasingly relying on it. In June, Malwarebytes revealed the existence of a campaign that used Flash-based ads served on a popular adult website. In late August, Fox-IT described a malvertising operation that affected several popular websites, including Java.com, Photobucket.com, TMZ.com and DeviantArt.com.
In terms of other recent threats targeting Mac OS users, FireEye warned earlier this week that a Windows backdoor used in numerous attacks by a certain threat actor group has been ported to Mac OS X and fitted with new features.















