A malvertising operation observed last year by advertising cybersecurity company Confiant exploited what turned out to be a zero-day vulnerability in the WebKit browser engine.
Confiant researchers discovered the security hole while analyzing a campaign carried out by a threat actor they call ScamClub. The group has been around for several years, launching malvertising attacks designed to redirect users to a wide range of scam websites promising prizes.
ScamClub specializes in high-volume operations — even if most of their payloads are blocked, a large number still reach users.
“Over the last 90 days, ScamClub has delivered over 50MM malicious [ad] impressions, maintaining a low baseline of activity augmented by frequent manic bursts — with as many as 16MM impacted ads being served in a single day,” Confiant said in a blog post on Tuesday.
The “allow-top-navigation-by-user-activation” attribute in WebKit’s iframe sandboxing feature is designed to prevent malicious redirections by only allowing a redirection to occur when it’s triggered by user actions (e.g. a click or a tap inside the frame).
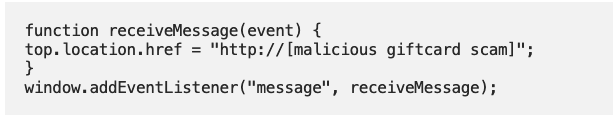
However, Confiant discovered that the ScamClub threat actor managed to bypass this iframe sandboxing mechanism by using an event listener for a “message” event. If the event listener picks up a message, it would trigger the redirect, which increases the chances of users being redirected to their scam websites without actually clicking inside their iframe to directly trigger the redirect.
“In modern web applications, messages are flying around all the time, usually with wildcard destinations, often on user interaction,” Confiant explained.
“Combined with ScamClub’s large volumes and broad targeting that hits dozens of different websites, it’s all about the increased efficacy of spawning a successful redirect — even if we’re talking about a single digit percentage increase, that can mean tens of thousands of impacted impressions over the duration of a single campaign,” the company added.
Confiant spotted the campaign exploiting the vulnerability in June 2020 and immediately reported its findings to Apple, whose Safari browser uses WebKit, and Google, whose Chrome browser on iOS also uses WebKit.
The issue was addressed in WebKit in December 2020, and Apple included the patch in the versions of WebKit delivered with updates released for iOS and macOS earlier this month. Apple tracks the issue as CVE-2021-1801 and claims to have addressed it with “improved iframe sandbox enforcement.”
Related: ‘LuckyBoy’ Malvertising Campaign Hits iOS, Android, XBox Users
Related: Exposed Twilio SDK Abused for Malvertising Attack
Related: WebKit Vulnerabilities Allow Remote Code Execution via Malicious Websites













