McAfee has shared details of a new botnet circulating on criminal forums, mostly out of Russia, which targets payment card terminals connected to Windows systems. The botnet, named vSkimmer, has been around since February and appears to be an ongoing project for the person selling it.
In a blog post discussing their research on vSkimmer, McAfee’s Chintan Shah says that vSkimmer is the successor to Dexter – financial malware responsible for the loss of nearly 80,000 credit card records and the successful breach of payment card data at scores of Subway restaurants in 2012. vSkimmer however has more functionality when compared to Dexter, mostly on a developmental level though. However, the author of vSkimmer says it’s easier to use.
In a forum post, vSkimmer is pitched as an advanced tool that will capture credit card data from systems running Windows that host payment processing software. vSkimmer will detect card readers and capture all of the track data collected, encrypt (Base64) the data and ship it off to a control server for later retrieval. Like Dexter, vSkimmer is said to be completely undetectable on the compromised host.
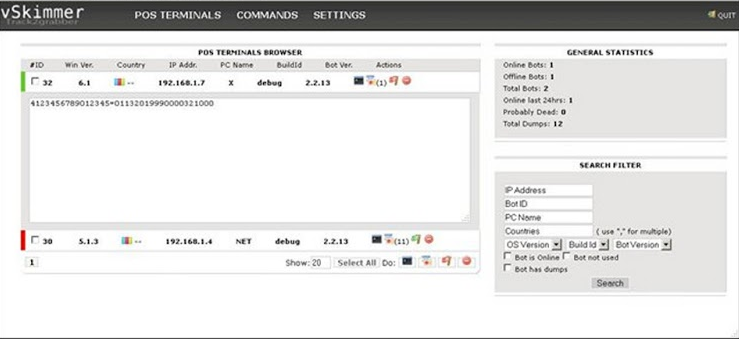
In the event that the Web is unavailable, vSkimmer will wait for a named USB device to be attached to the system, and automatically dump the collected data to the removable device. In addition, it uses a whitelisting routine to look for actionable processes, by checking each process ran on the system that isn’t on the ignore list and using pattern matching to extract the card’s Track 2 data. Track 2 is where the card number, three-digit CVV code, and expiration date are stored.
If present in the terminal software, the person selling vSkimmer says it will also ferret out any additional data, including names and PINs, but McAfee’s research didn’t confirm this.
“VSkimmer is another example of how financial fraud is actively evolving and how financial Trojans are developed and passed around in the underground community. This botnet is particularly interesting because it directly targets card-payment terminals running Windows,” Shah explained in his post.
Additional technical information is available here.
















