Verizon Wireless appears to be the latest victim of a vishing attack, with a well-crafted scam targeting its customers and looking to capture sensitive customer information.
In this current attack which started today, the attackers are using automated phone calls to direct people to the website “www.myverizonoffer.com” in order to claim a reward. “Simply login to your account to redeem your one hundred dollars,” a male recorded voice states. “At Verizon we care about you. Thank you, and have a nice day,” the message concludes. The caller-id displayed (which could easily be spoofed) was a 303-731-XXXX number.
While the attack is targeting Verizon Wireless customers in hopes that they will login to the fake customer portal, the attackers are calling what appears to be random numbers, including non-Verizon numbers of people who may not be customers.
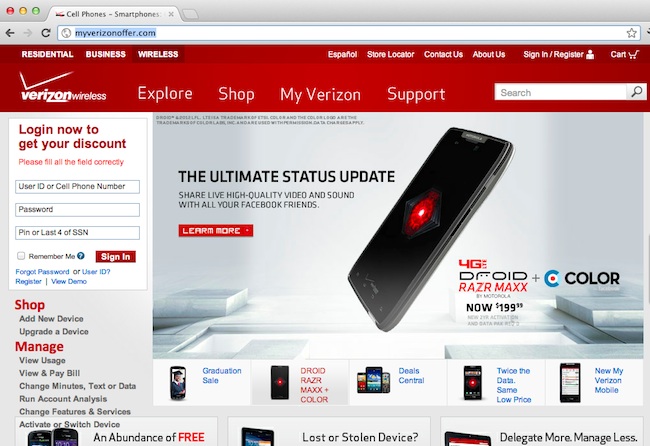
Interestingly, the well-designed phishing page asks for phone number or user name, along with password and the last four digital of the user’s social security number—a field that is not required to login to the real Verizon Wireless site. As is the case with most good phishing sites, the site is a near replica of the VerizonWireless.com site and loads much content from the real site, including trust marks and “seals” to help prove the site’s authenticity.
If an unsuspecting user visits the fraudulent site, entering any value into the login fields will result in a “success” – showing that the cybercriminals are simply capturing all data submitted to their rogue login form.
After submitting login data, users are presented with the message, “Congratulations! You have successfully applied for your discount,” with a button below labeled “Go to my account,” which, if clicked, actually directs users to the legitimate Verizon Wireless website.
Looking into the domain itself, “www.myverizonoffer.com” was actually registered today, indicating that the attackers had this planned ahead of time, and waited until the last minute to register the domain and activate the site. (Domains registered that contain a large brand name and/or trademark are likley to be caught ahead of time.)
In order to see if a spam campaign may also be associated with the attack, SecurityWeek reached out to anti-spam technology firm Cloudmark to see if they had seen any activity this morning that may have been attempts to direct users to the “Myverizonoffer.com” site. As of yet, they have not seen such spam showing up. This could be an effort to further stay below-the-radar as long as possible, as many anti-phishing and fraud detection services parse spam messages in order to identify and shut down phishing sites.
“The myverizonoffer.com appears to be solely a vishing scam at this point,” said Mary Landesman, a senior security researcher at Cloudmark. “Essentially, the scammers use VoIP to place calls to numbers they either guessed through brute/dictionary force (aka war-dialing) or which they obtained from stolen call center lists.”
While in this case the voice appears to be a recording of a real person’s voice, Landesman added that often, these types of calls are synthesized and recorded using text to voice recognition software.
“Since the call isn’t placed over traditional landline infrastructure it’s harder for authorities to trace,” she added.
“Myverizonoffer.com is hosted by Yahoo, which happens to be a bit ‘unfriendly’ when it comes to reporting phishing/abuse sites they are hosting – i.e. you have to sign in with a Yahoo account in order to report the abuse.”
Landesman also pointed to some interesting research on the current threat landscape as it relates to vishing. According to Pindrop Security’s State of Phone Fraud Report, vishing increased by 52% in the second half of 2011. Nearly 190k fraudulent calls were observed in December 2011. The report also states that “All five of the largest national financial institutions, and 30 of the top 50, were targeted by vishers during the second half of 2011. On average, fraudsters used at least 200 numbers to contact customers assuming the identity of such prominent institutions.”
As of the time of publishing, the site was still active.
Update: Checking on the site again at 10PM ET, the domain appears to be offline and Firefox and Google Chrome users will likely experience a “Web Forgery” warning if trying to access the site.















