The United States this week announced that it seized a total of 92 domain names that an Iran-linked adversary was leveraging in a global disinformation campaign.
Although four of the domains pretended to be genuine news outlets, they were controlled by Iran’s Islamic Revolutionary Guard Corps (IRGC) to spread Iranian propaganda targeting the United States, while the remaining websites were spreading propaganda to other countries.
The manner in which these domains were being used was in violation of sanctions the U.S. imposed on both the government of Iran and the IRGC.
As of April 2019, the United States has designated the IRGC as a foreign terrorist organization. The organization was found to have provided material support to terrorist groups such as Hizballah, Hamas, and the Taliban.
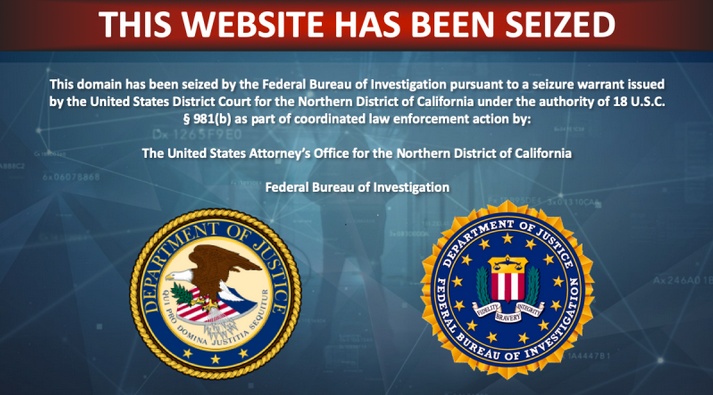
On October 7, pursuant to a seizure warrant, the United States seized 92 domain names that were being operated in violation of federal law. Four of these were seized pursuant to the Foreign Agents Registration Act (FARA), which requires the submission of periodic registration statements about activities and income.
“The four domains purported to be independent news outlets, but were actually operated by or on behalf of the IRGC to target the United States with pro-Iranian propaganda in an attempt to influence the American people to change United States foreign and domestic policy toward Iran and the Middle East,” the U.S. Department of Justice says.
These domains, the DoJ explains, targeted an audience in the U.S. without proper registration pursuant to FARA and also failed to inform the audience that the IRGC and the government of Iran were in control of the published content.
Also masquerading as news outlets, the remaining 88 domains targeted audiences in Western Europe, the Middle East, and South East Asia, spreading pro-Iranian disinformation.
All of the domains were found to be owned and operated by companies in the U.S., but the government of Iran and the IRGC used them without a license from the Office of Foreign Assets Control (OFAC). Pursuant to the International Emergency Economic Powers Act (IEEPA), a license is required to provision services to the government of Iran.
The activity associated with these domains was initially reported on in 2018, but the Department of Justice has now linked it to the IRGC, John Hultquist, Senior Director of Analysis, Mandiant Threat Intelligence, said in an emailed comment.
“The DOJ has just linked Iranian information operations that FireEye publicly reported in 2018 to the Islamic Revolutionary Guard Corps, Iran’s aggressive security service. The IRGC is very comfortable with asymmetric tools and they have increasingly adopted cyber capabilities as a means to disrupt and manipulate their enemies abroad. Iran has become a prolific actor in the information operations space and similar to their cyberattack capability, they have evolved over a series of brash operations,” Hultquist said.
Related: Smoke and Mirrors – Hack-for-Hire Group Builds Fake Online Empire
Related: Twitter Removes Iran-Linked Accounts Aimed at Disrupting U.S. Presidential Debate













