The U.S. State Department and the National Counterintelligence and Security Center (NCSC) on Friday issued a warning over the use of commercial surveillance tools.
The one-page document says governments and other entities have been using spyware sold by companies and individuals. The spyware can typically be used to record audio, track a device’s location, and access all of the content stored on a phone.
“Journalists, dissidents, and other persons around the world have been targeted and tracked using these tools, which allow malign actors to infect mobile and internet-connected devices with malware over both WiFi and cellular data connections. In some cases, malign actors can infect a targeted device with no action from the device owner. In others, they can use an infected link to gain access to a device,” the alert reads.
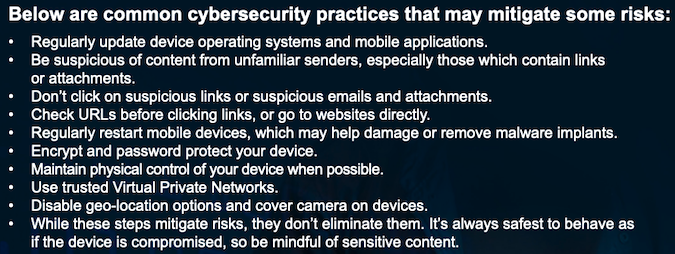
The alert also includes some general recommendations for mitigating “some risks” posed by surveillance tools. However, the government warned that “it’s always safest to behave as if the device is compromised.”
The NCSC also noted in a tweet posted on Friday that “commercial surveillance tools are also being used in ways that pose a serious counterintelligence and security risk to U.S. personnel and systems.”
While the document does not name any specific spyware, it likely refers to the infamous tools made by the controversial Israel-based NSO Group.
The warning comes after the Biden administration announced in November new export limits on the NSO Group — to limit its access to U.S. components and technology. The measures were part of efforts to promote human rights in U.S. foreign policy.
Related: Apple Slaps Lawsuit on NSO Group Over Pegasus iOS Exploitation
Related: Google Says NSO Pegasus Zero-Click ‘Most Technically Sophisticated Exploit Ever Seen’
Related: Polish Leader Admits Country Bought Powerful Israeli Spyware













