A team at Temple University in Philadelphia has been tracking worldwide ransomware attacks on critical infrastructure, and anyone can request access to the data.
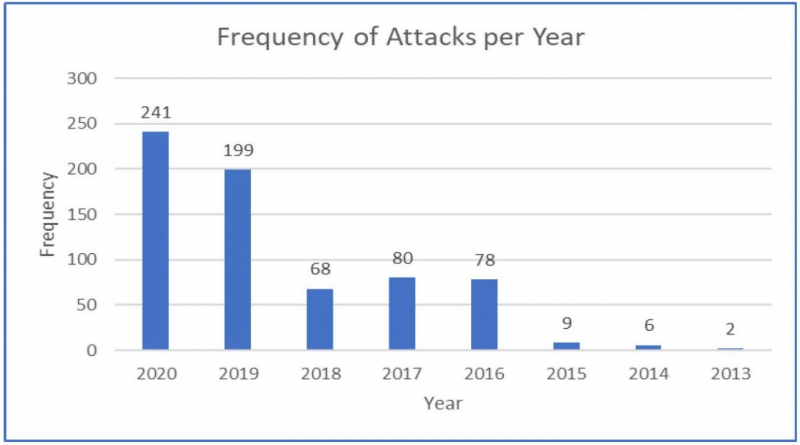
Work on this project, described as a repository of critical infrastructure ransomware attacks (CIRWA), started in September 2019. As of August 2020, the database includes over 680 records of ransomware attacks documented since November 2013.
The repository, offered for free as a Microsoft Excel file, stores information on incidents described by the media and cybersecurity companies.
The information includes the name of the targeted organization, the year the attack was launched, the date when the attack started, location of the targeted organization, the targeted sector, duration of the attack, the ransomware family that was used, the ransom amount, the payment method, whether the amount was paid, how much was paid, the source of the information, and related incidents. Based on the type of ransomware that was used, there are also links to the MITRE ATT&CK framework.
An analysis of the data currently shows that government facilities were the most targeted type of critical infrastructure — followed at a distance by education and healthcare — and Maze was the most common ransomware strain. It’s worth noting that the project tracks incidents affecting critical infrastructure as defined by the U.S. Department of Homeland Security.
The most commonly observed duration of a ransomware attack is one week or less, and the most commonly demanded ransom amount is $50,000 or less, but there are 13 known incidents where the attackers demanded more than $5 million.
Ransomware attacks on critical infrastructure – click on the image for the full summary
Aunshul Rege, associate professor in the Department of Criminal Justice at Temple University, leads the project, which is funded by her National Science Foundation (NSF) CAREER award. One of the main contributors to the project is her graduate student, Rachel Bleiman, a PhD student in the university’s Criminal Justice program.
“We started with the goal of just providing a dataset based on open-source information on disclosed CIRW incidents,” Rege told SecurityWeek. “My team and I struggled to find datasets that are free/no strings attached in the [critical infrastructure] space, which could be used by researchers/educators (like myself) and also by students.”
She added, “This dataset was driven by the need to contribute to the education/academic space to help educators and students. My team and I were collecting data for my NSF CAREER grant anyway, so we decided to rehash it in a structured way to share with the academic community. We started the CIRW dataset in Sep 2019 with 162 incidents. Today we have 687 incidents!”
Learn more about critical infrastructure threats at SecurityWeek’s 2020 ICS Cyber Security Conference and SecurityWeek’s Security Summits virtual event series
According to Rege, a lot of people have found the data useful. She says it has so far been requested by educators in higher education for class projects, research and publications; undergrad students for course projects; grad students for dissertation literature review; government representatives for ICS training classes, raising awareness, and assessing internal responses to critical infrastructure ransomware attacks; researchers for trends and patterns in TTPs across ransomware strains, comparing the data to their own internal datasets, and threat modeling and intelligence; and representatives of the private sector for training, threat intelligence, risk and statistical analysis, raising awareness, and overviewing current trends.
Anyone can request the data for free and Rege says they have approved nearly all the requests they’ve received to date.
“We do get some [requests] that are from personal email addresses (gmail, protonmail, etc), which we follow up on. Two other reasons why we want to keep track of who is using the dataset is so that we can (i) get feedback and (ii) potentially develop collaborative research projects,” Rege explained.
The maintainers of the project have been making improvements based on the feedback they have received from the community, such as mapping attacks to the MITRE ATT&CK framework.
Related: Seven Ransomware Families Target Industrial Software
Related: Honda Ransomware Confirms Findings of Industrial Honeypot Research