Tens of cybersecurity companies expose a large number of assets to the internet, according to a study conducted recently by attack surface management firm Reposify.
It’s not uncommon for major companies to unwittingly expose databases and other assets, but a study conducted by Reposify over a two-week period in January showed that 35 multinational cybersecurity companies and their more than 350 subsidiaries hosted over 200,000 exposed assets. These assets included databases, remote access sites, and cloud services.
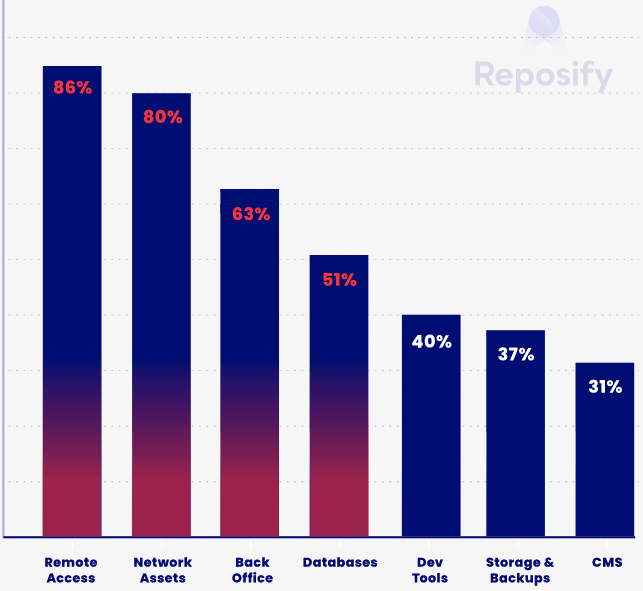
Reposify’s analysis showed that 86% of these companies have at least one exposed remote access service, 80% expose network assets, and 63% expose back office internal networks. Just over half of the cybersecurity firms have at least one exposed database.
In a vast majority of cases, companies exposed platforms such as Nginx, Apache, OpenSSH, IIS and Portmap, which are “highly sensitive, and the consequence of a breach is severe — particularly in the case of the cybersecurity industry.”
As for exposed remote access protocols, 90% of companies exposed OpenSSH, followed by RDP (47%), Telnet (33%), and SMB (30%).
The study showed that more than two-thirds of companies exposed PostgreSQL databases, and half exposed Oracledb databases.
Many cybersecurity firms and their subsidiaries also appear to expose storage and backup systems (FTP, S3), and development tools (Express, Jenkins, Tableau Server).
Nearly every cybersecurity company seems to host exposed assets on the AWS cloud platform (97%), followed by Azure (82%) and Google Cloud (76%).
[ You can learn more about attack surface management at
SecurityWeek’s Attack Surface Management Summit – available on demand ]
One concerning finding is that — except for storage and web assets — a majority of exposed services are in the organization’s “unofficial perimeter,” which means they are less likely to be monitored.
“Services under unknown perimeters are less likely to be known, and often represent shadow IT, unknown risks, or flag a possible backdoor malactors can use to access a company’s assets,” Reposify said in its report.
More than 40% of the vulnerabilities affecting exposed services have a “high” or “critical” severity rating.
“Just one of these statistics is concerning enough – but the combination points to a sincere need for the industry to better practice what it preaches,” Reposify said.
Related: Over 28,000 Vulnerabilities Disclosed in 2021: Report
Related: Telemetry Report Shows Patch Status of High-Profile Vulnerabilities














