New Report Shows Advanced Cyber Attacks Occur Up To Once Every Three Minutes
Three minutes – that’s all it takes.
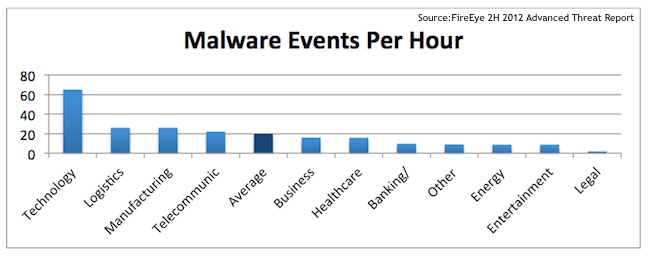
According to FireEye’s ‘2H 2012 Advanced Threat Report’, in the second half of last year, individual enterprises were hit with a “malware event” every three minutes, ranging from a user receiving a malicious email to an employee clicking on a link to an infected website to a compromised machine making a call back to a command-and-control server. Ironically, it was the tech industry that was hit the hardest, most likely due to the value of their intellectual property, the report said.
“What this says about the attackers is they know which companies have the greatest tangible intellectual property right now,” Ali Mesdaq, senior security researcher at FireEye, told SecurityWeek. “Technology companies have the type of IP [intellectual property] that can be taken easily and leveraged quickly in comparison to some other verticals.”
The figure is based on data gathered from FireEye customers on 89 million malware events. The most common avenue of attack is spear phishing, with business-related terms unsurprisingly playing a role in the lures.
“When sending spear phishing emails, attackers opt for file names with common business terms to lure unsuspecting users into opening the malware and initiating the attack,” according to the report. “These terms fall into three general categories: shipping and delivery, finance, and general business. The top phrase in malware file names, for example, was ‘UPS’.”
Other commonly cited words in malicious emails were: details, documents and FedEx. The most common malicious file names included Details.zip and UPS_document.zip. Zip files were the primary delivery method for attackers, representing the method in 92 percent of attacks. This is no accident – hackers know Zip files are common in the business world.
“Attackers know that not many people are going to be clicking .exe extensions as often as a .zip,” Mesdaq said. “Filtering policies now have to be created much more carefully because attackers know that a block on all .zip files is not very likely.”
Attackers are also turning to DLL files in a bid to evade detection.
“By using DLLs, the malware can establish persistent control as every time a vital, commonly used application like Internet Explorer is used the malicious payload is loaded automatically—without any user involvement or awareness,” the report notes. “If the malware were dependent on user commands to execute a malicious payload, chances are much more likely that users would get suspicious and not take the step necessary for the malware to operate.”
Malware authors are also taking steps to evade detection by programming their creations to detect when they are in a sandbox. A recent example of this is Trojan.APT.BaneChant, which is designed to execute only after it has detected three mouse clicks, which is interpreted as an indicator of human interaction.
“Vendors and analysts need to constantly be following the evasion techniques malware authors are using,” Mesdaq said. “The legacy techniques range from looking for various process names, hardware information, and registry settings. The newer techniques are more related to user interaction or deeper checks on the system looking for specific applications installed.”
















