Spam campaigns have evolved from sending a low number of messages for long periods of time to sending a high volume of emails over a short time span, which improves delivery rates before protection mechanisms can be triggered, Cisco Talos researchers warn.
Called “hailstorm” spam, the new type of spam relies on the use of a large number of sender IP addresses from all around the world. While traditional campaigns, called snowshoe attacks, show a query rate of 35 queries per hour, the DNS query volume during hailstorm attacks spikes to over 75K queries per hour, researchers say.
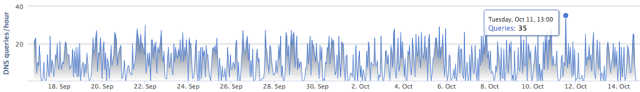

Charts of DNS query volume patterns for traditional snowshoe spam (Top) vs. Hailstorm Spam (Bottom) [Image Credit: Cisco]
The analysis of recent campaigns has shown that hailstorm spam is being sent from all around the world, with the United States, Germany, Netherlands, the United Kingdom and Russia being the top five countries in terms of sent emails. What’s more, these attacks also involve domains registered at a wide array of Top Level Domains (TLDs), Cisco security researchers reveal.
The initial hailstorm spam campaigns were focused on advertising products such as home-surveillance systems, flashlights, dietary supplements, and other items, and different types of services, as well as on generating sponsored traffic. However, the new attack method was used for more damaging purposes than just generating traffic to affiliate pages, as malware and phishing entered scene.
The Necurs botnet, Cisco says, is using hailstorm tactics to spread malware. Cisco researchers observed a message supposedly coming as a response to a complaint filed with the United Kingdom’s Companies House, but which distributed the TrickBot banking Trojan via a malicious attachment.
While this hailstorm malware campaign shared similarities with other similar attacks, such as the delivery of the whole campaign in a very short burst, it also showed significant differences from typical hailstorm spam campaigns, researchers say. Messages were sent from a wider range of IPs, including some addresses that did not resolve to the domain used in the From header, and the messages were more in line with traditional spam and bot behavior.
The security researchers also managed to tie hailstorm campaigns with bursts in DNS queries with an intensity of 9,000+ queries per hour at their peak(s). “The initial spike in a hailstorm campaign stems from mail server activity caused by an influx of emails. One way to understand the life cycle of a hailstorm campaign is to look at how many mail servers are targeted with a given domain,” the researchers explain.
By looking at the mail servers targeted by a sample of 475 hailstorm domains, Cisco also determined that servers in the United States are targeted the most compared to other countries.
“As outlined in the examples, hailstorm comes in several flavors. We expect to see it evolve over time as anti-spam systems make it harder and harder for spammers to deliver their payload,” Cisco says.









