Source code belonging to tens of companies, including several major organizations, has been leaked online after it was found on unprotected DevOps infrastructure.
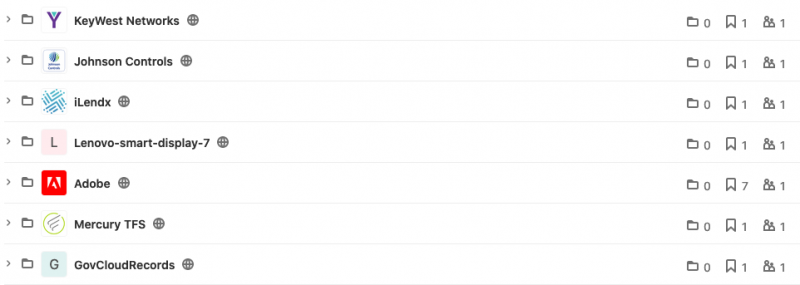
Swiss-based IT consultant Till Kottmann has posted a list of roughly 50 companies that at some point exposed source code. For some of the impacted organizations the code has been removed from the repository, but in many cases it’s still available.
Kottmann told SecurityWeek that the source code they’ve made public, much of which appears to be proprietary, mostly comes from improperly configured or exposed DevOps infrastructure. The researcher says the information mainly originates from SonarQube instances, but also from GitLab and Jenkins.
“Some of the things are also sent to me by various sources,” Kottmann explained. “I usually do not know how they obtained the code.”
The list of impacted companies appears to include Microsoft, Adobe, Johnson Controls, GE, AMD, Lenovo, Motorola, Qualcomm, Mediatek, Disney, Daimler, Roblox, Nintendo and various organizations in the software, hardware, healthcare, finance, automotive, travel and industrial sectors.
Microsoft did not want to comment on the source code leak. Adobe told SecurityWeek that it’s aware of the website hosting the source code and it’s working on having the content removed. The Adobe source code is still online at the time of publishing.
“We have no evidence to suggest that any Adobe systems or customers have been compromised due to this issue,” the company stated.
Kottmann said they try not to release anything that could put individuals in danger and they attempt to censor any credentials they find before making the code public. They also noted that impacted vendors have not been notified, unless important information (e.g. healthcare information) has been identified in the exposed files, in which case the data will not be made public and the vendor will be contacted.
“There are multiple aspects to this [project],” Kottmann explained. “It will hopefully show some companies that their own infrastructure also needs to be protected. I am also very curious and so are many other people, and this gives an interesting inside view into how (unfortunately often badly) proprietary projects are built.”
“In the case of things like Mediatek or Qualcomm this is obviously also about allowing people to do with their (mobile) devices what they please, and make things like custom roms easier,” the researcher added. “Lastly there is also, at least for some of these releases, certainly a political aspect that plays a role, but the other reasons overshadow this mostly.”
Related: BlueLeaks: Data From Hundreds of Law Enforcement Organizations Leaked Online
Related: Hackers Leak Data Stolen From UK Electricity Market Administrator Elexon
Related: Unprotected Database Exposed 5 Billion Previously Leaked Records














