UK-based cybersecurity company Sophos has warned customers that a new zero-day vulnerability affecting some of its firewall products has been exploited in attacks.
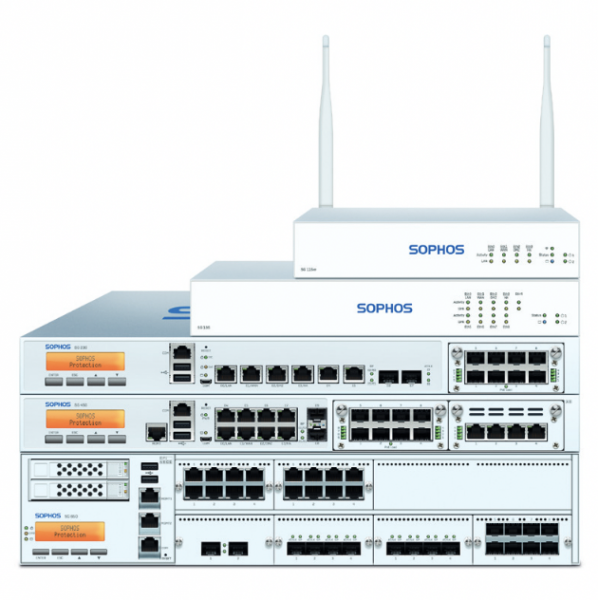
According to an advisory published on Friday, version 19.0 MR1 (19.0.1) and older of Sophos Firewall are affected by a critical vulnerability that can be exploited for remote code execution. The flaw, tracked as CVE-2022-3236, exists in the product’s User Portal and Webadmin components.
 The security hole has been patched and customers whose products are configured to automatically install hotfixes — this is the default setting — don’t have to take any action. The company has also provided instructions for checking if the patch has been applied.
The security hole has been patched and customers whose products are configured to automatically install hotfixes — this is the default setting — don’t have to take any action. The company has also provided instructions for checking if the patch has been applied.
“Sophos has observed this vulnerability being used to target a small set of specific organizations, primarily in the South Asia region. We have informed each of these organizations directly,” the company said.
Entities in South Asia have been targeted in several cyberespionage campaigns in recent years, including some attributed to Chinese threat actors.
In addition to providing a patch, Sophos has informed customers that attacks can be prevented by ensuring that the user portal and webadmin interfaces are not exposed to the WAN. The Sophos Central console or a VPN are recommended for remote access and management.
A researcher from Japan pointed out that a Shodan search shows more than 200,000 internet-exposed Sophos appliances around the world.
The US Cybersecurity and Infrastructure Security Agency (CISA) has rushed to add CVE-2022-3236 to its catalog of known exploited vulnerabilities, instructing federal agencies to address the flaw by October 14.
This is the fourth Sophos product vulnerability added to CISA’s catalog, which includes CVE-2020-25223 (Sophos SG UTM), CVE-2020-12271 (XG Firewall), and CVE-2022-1040, a Firewall vulnerability added earlier this year.
In the case of the zero-day discovered this year, Sophos again said it had been exploited against a small set of specific organizations mainly located in South Asia. Incident response firm Volexity linked the attacks to a sophisticated Chinese APT group tracked as DriftingCloud.
Volexity said it had seen attacks aimed at organizations, including governments, in Afghanistan, Bhutan, India, Nepal, Pakistan, and Sri Lanka.
Related: Malware Delivered to Sophos Firewalls via Zero-Day Vulnerability
Related: Meta Disrupted Two Cyberespionage Operations in South Asia
Related: Details Disclosed for Critical Vulnerability in Sophos Appliances













