A hashed password list containing some 6.5 million records has been uploaded to a Russian forum earlier this week. An expert consulted for the story says that there are indications the passwords were taken from the corporate social network LinkedIn, and this has since been confirmed with LinkedEd.
Update: LinkedIn has confirmed that customer passwords have been compromised. The company posted a blog on the incident here with additional details.
The story appeared Wednesday on Dangens IT (www.dangensit.no). Per Thorsheim, a reported password expert and consultant, told Dangens that the lists were uploaded in an effort to crowd source their cracking. It was on his information that the link to LinkedIn was established. Listed on Twitter as @thorsheim, a CISSP from Norway, he is a password researcher with 12 years of experience and also organizes the Passwords^XX conferences.
 According to the reports from those working the list, some 300,000+ passwords have been cracked. Examination of the cracked hashes that have been posted to InsidePro’s forums shows several passwords using the phrase LinkedIn in some fashion.
According to the reports from those working the list, some 300,000+ passwords have been cracked. Examination of the cracked hashes that have been posted to InsidePro’s forums shows several passwords using the phrase LinkedIn in some fashion.
It’s worth repeating that aside from this, there is no evidence to confirm that the social network was breached or suffered some other type of security incident.
What is publically available are the password hashes, usernames were not released with the list. But it is unknown if the originators of the list simply stripped the usernames out in order to make cracking the hashes easier.
It’s also worth noting that the list contains 6.5 million records, whereas LinkedIn boasts more than 100 million registered users – so this is only a fraction of their membership if the passwords did indeed come from the site.
SecurityWeek has contacted LinkedIn who is investigating the claims, and said they would get back to us.
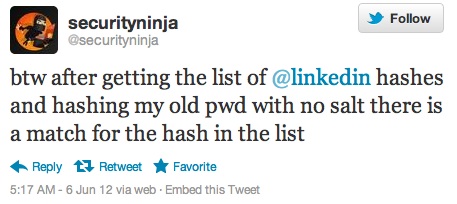
Also on Twitter, @Securityninja Tweeted, “btw after getting the list of @linkedin hashes and hashing my old pwd with no salt there is a match for the hash in the list”.
For now, it is wise to play things safe and change your LinkedIn password. If that password is used anywhere else, those accounts will need to be updated as well. A translation of the original story, the source of the rumor itself, is here.
Related: Combating Password Cracking Tools in the Enterprise
Related: How Passwords Are Cracked and How You Can Keep Them Safer













