RSA, The Security Division of EMC on Wednesday launched RSA Security Analytics, a new unified platform that the company hopes will be the cornerstone of next generation security operations centers.
According to the company, the platform is designed to leverage the power of Big Data to provide visibility and context in order to help identify and defend against advanced threats.
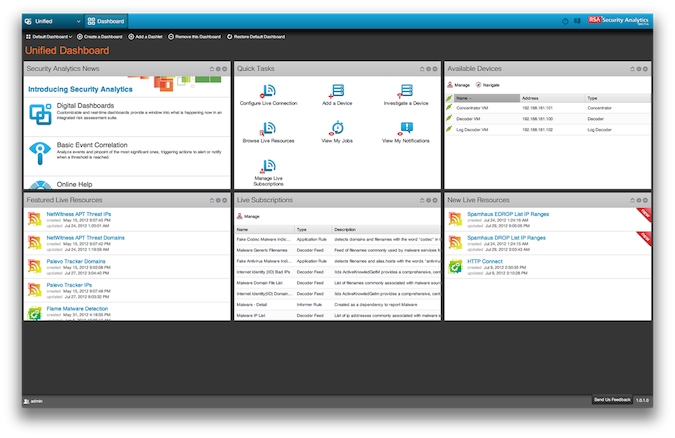
RSA Security Analytics is built on the architecture of RSA NetWitness, technology the company gained as a result of its 2011 acquisition of NetWitness. RSA Security Analytics fuses SIEM, Network Forensics, & Big Data analytics, the company said.

The move to integrate big data into its latest security analytics offering is hardly surprising. Earlier this month, the veteran security firm shared its thoughts on Big Data’s place in the security world, saying it would transform IT security as the industry shifts towards intelligence-driven security models.
“Organizations will shift to using big data analytics within the next few years to intelligently assess threats and risks and make better security decisions,” RSA said in a security brief released Jan. 17. The intelligence gleaned from unstructured data will allow enterprises to drive major changes in conventional security controls such as anti-malware, data loss prevention, and firewalls, RSA said at the time.
RSA claims that current security technologies, including SIEM tools, cannot provide deep enough visibility into today’s threats, and often cannot scale to today’s analytic needs.
The integration of Big Data platforms and analytics into security tools gives a significant advancement to how security is performed, RSA said.
According to the company, RSA Security Analytics is designed to deliver:
• Quick Capture and Analysis – Security-relevant data, including full network packets, logs, and threat intelligence, are captured and quickly analyzed to speed up the detection of potential threats.
• High Powered Analytics – Enables much larger-scale collection of data and empowers new analysis methods over that of traditional SIEM-based approaches to security.
• Integrated Threat Intelligence – Helps organizations operationalize the use of threat intelligence feeds to accelerate detection and investigations of potential attack tools and techniques targeting the enterprise.
• Context for Threats – Through integrations with the RSA Archer GRC platform and RSA Data Loss Prevention (DLP) suite, and by fusing data produced by other products, analysts can use business context to prioritize and allocate resources to the threats which pose the greatest risk.
• Malware Identification – Using a variety of investigative techniques, the solution identifies a much wider range of malware-based attacks.
• Automates Compliance Reporting – Helps enable compliance as an outcome of good security practices.
RSA’s announcement of integrating Big Data into its security analytics platform came on the same day that IBM made a similar announcement. IBM, in an effort to help customers detect threats hidden within the massive amounts of data that reside within enterprise walls, on Wednesday announced “IBM Security Intelligence with Big Data”, an offering that combines security intelligence with big data analytics capabilities.
“Marrying intelligence-driven security with Big Data analytics has the potential to help enterprises address the complex problem of advanced threats and thus meet a significant need in the marketplace,” Jon Oltsik, Senior Principal Analyst, Enterprise Strategy Group said in a statement.
RSA Security Analytics is available immediately worldwide as a software solution or as an appliance.













