Prodaft security researchers exploited a vulnerability in the recovery servers used by the Conti Ransomware-as-a-Service (RaaS), which allowed them to gain insight into the inner workings of the ransomware.
The flaw also allowed the researchers to identify the real IP addresses of the hidden service hosting the recovery website, including 20 IPs communicating with the Conti servers, and two Tor entry nodes used for the recovery service, all of which were reported to the authorities.
Furthermore, Prodaft discovered victim chat sessions that allowed them to identify accounts used when extorting victims’ data, including connecting IP addresses and the employed software. The investigation also revealed the use of the same Bitcoin wallet addresses for multiple victims.
In a new report, Prodaft’s security researchers provide technical details related to the inner workings of Conti, and also show the close connection between Conti and Ryuk, essentially saying that these appear to be one and the same ransomware family.
“The data contained in this report will help law enforcement authorities act against the Conti ransomware group and its affiliates, which should result in a drastic reduction in the number of victims in the near future,” the cybersecurity firm wrote in its report.
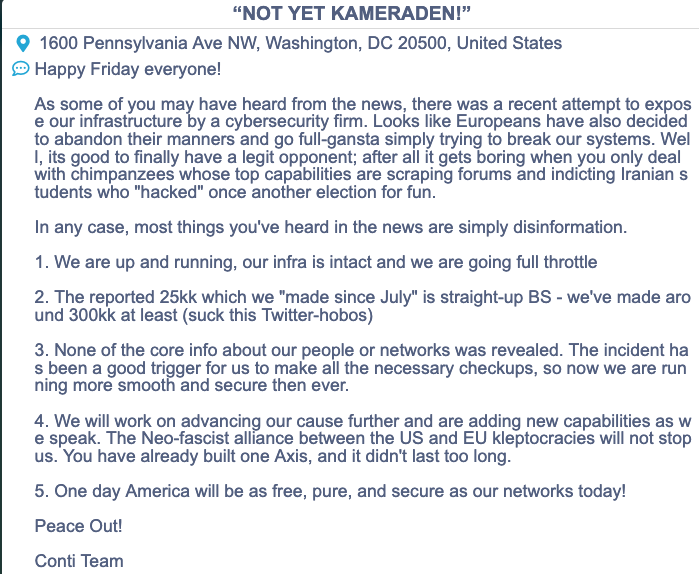
In a statement published on their Tor-based leak website, Conti operators confirmed the breach, but claimed that no important information about its members or networks was exposed.
Believed to be the successor of the Hermes ransomware, Ryuk first emerged in 2018, and has shown a close connection with the TrickBot malware, supposedly being operated by the same cybercriminals.
Conti was first spotted in 2020 and managed to become a prevalent threat within months, with over 400 organizations worldwide likely impacted by May 2021. In September, a U.S. government alert warned of an increase in Conti ransomware attacks.
Operating under the RaaS business model, where affiliates share up to 30% of the received payments with the ransomware operators, Conti has helped the perpetrators make over $25 million to date, the security researchers say.
The Conti affiliate panel provides access to an executable generator, a decryption application, a payment gateway for the victims, commission rate calculator, monitoring tools, and secure chat for communication with the victim.
“These tools are designed with non-technical users in mind. Cybercriminals no longer need a great deal of technical expertise to run successful attack campaigns. Instead, they maximize profit using psychological tactics like extortion and victim shaming,” Prodaft explains.
Prodaft also notes that Conti is targeting publicly known vulnerabilities such as PrintNightmare (CVE-2021-1675, CVE-2021-34527, and CVE-2021-36958) and FortiGate remote code execution bugs (CVE-2018-13379 and CVE-2018-13374).
Related: U.S. Issues Conti Alert as Second Farming Cooperative Hit by Ransomware
Related: Researchers Estimate Ryuk Ransomware Operations to Be Worth $150 Million













