A researcher has made public technical details, a video and proof-of-concept (PoC) exploit code for an unpatched local privilege escalation (LPE) vulnerability affecting Windows.
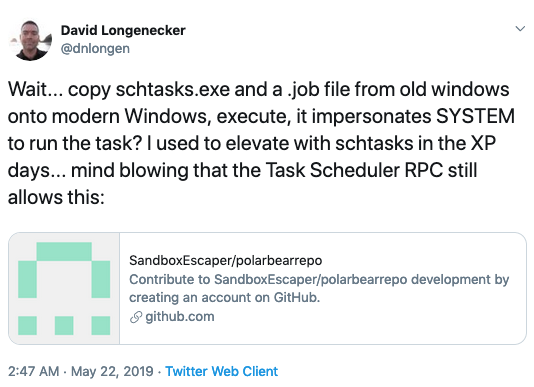
The flaw, disclosed by a researcher who uses the online moniker SandboxEscaper, is related to discretionary access control lists (DACL) and the Task Scheduler, and the exploit has been confirmed to work reliably on a fully patched Windows 10 machine, including 64-bit systems.
The vulnerability allows an attacker with limited privileges to change permissions for a specified file by importing a .job file into the Task Scheduler using schtasks.
SecurityWeek has reached out to Microsoft for comment and will update this article if the company responds. Unless in-the-wild exploitation is detected, the company will likely address the flaw with Patch Tuesday updates.
This is not the first time SandboxEscaper has released the details of a Windows LPE vulnerability before informing Microsoft or giving the company time to release a patch. The expert, who is apparently frustrated (among other things) with Microsoft’s vulnerability reporting process, previously disclosed several other privilege escalation flaws, including another one related to the Task Scheduler in Windows.
One of the vulnerabilities whose details were made public last year by SandboxEscaper ended up being exploited in attacks by a threat group tracked as PowerPool.
SandboxEscaper claims to have discovered four other unpatched flaws, including three LPE issues that allow an attacker to execute arbitrary code with SYSTEM privileges and one sandbox escape.
The researcher has offered to sell exploits, but only to “non-western people” and not “for less than 60k.”
UPDATE. Microsoft has sent SecurityWeek the following statement:
“Microsoft has a customer commitment to investigate reported security issues and we will provide updates for impacted devices as soon as possible. We urge finders to practice coordinated vulnerability disclosure to reduce the potential risk to customers.”
Related: Third-Party Patch Released for Windows Zero-Day
Related: Exploit for New Windows Zero-Day Published on Twitter
Related: Microsoft Patches Windows Zero-Day Disclosed via Twitter














